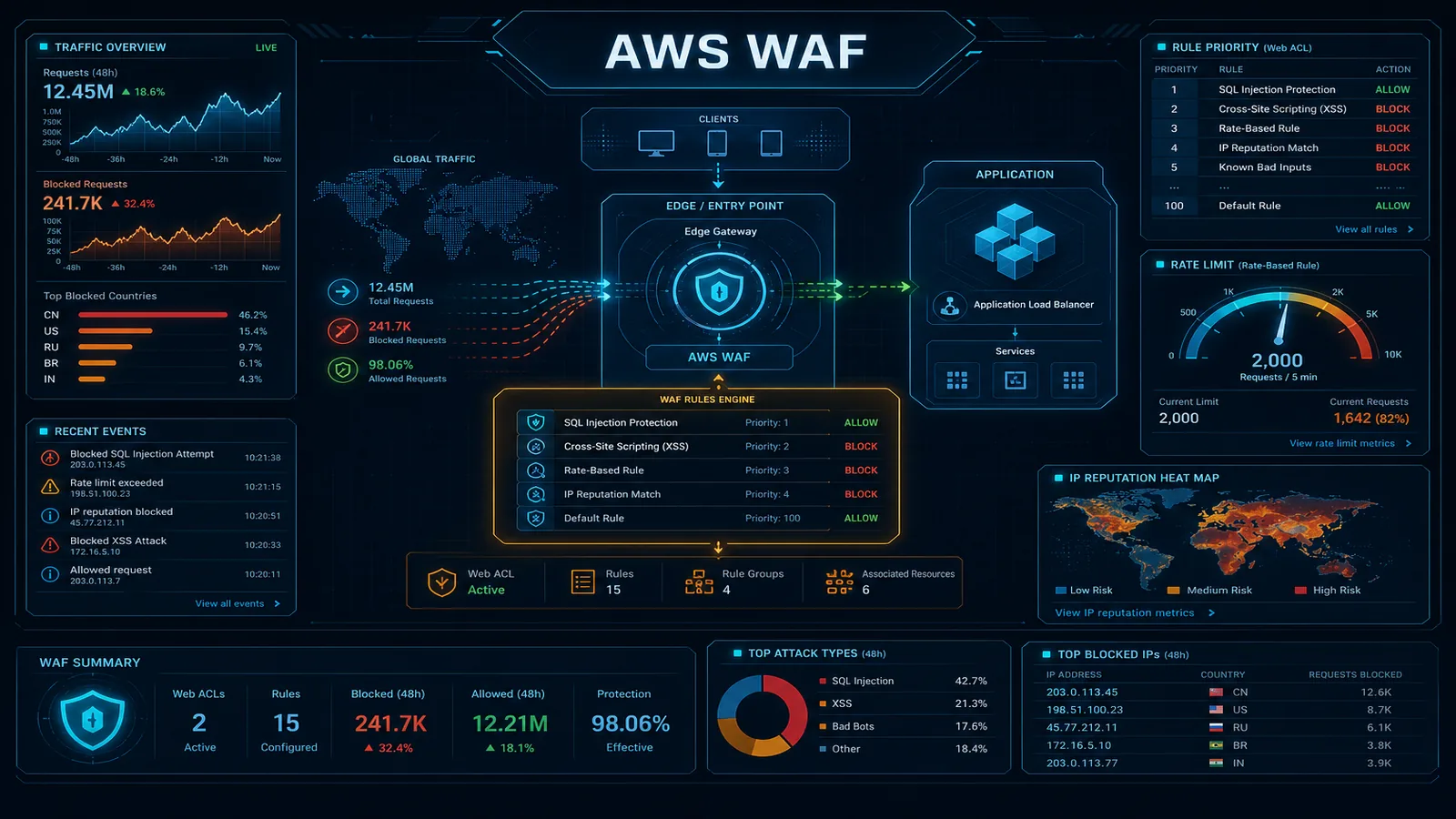
AWS WAF: Web Application Firewall Configuration for Production
A practical guide to AWS WAF for production web applications — managed rule groups, custom rules, rate limiting, bot control, and the layered defense strategy that protects without blocking legitimate traffic.