
10 AWS Cloud Security Best Practices: An Implementation Guide for 2026
Most AWS security breaches aren't caused by AWS failures — they're caused by misconfiguration. Here are 10 concrete best practices to harden your AWS environment in 2026.
Governance & Multi-Account
Org-wide guardrails, account isolation strategy, and continuous compliance monitoring as code.
Multi-account is where compliance scope is either won or quietly lost. The guides below cover Control Tower, landing-zone topology, drift detection, Well-Architected reviews, and CI/CD that does not become an unaudited backdoor into prod. With AWS Audit Manager closed to new customers from 30 April 2026, evidence collection now consolidates onto AWS Config conformance packs (regulator-aligned control sets, deployable across an Organization) and Security Hub Essentials on its resource-based pricing — the pairing we now recommend for every new engagement.
Part of the AWS Security & Compliance hub.
Guides

Most AWS security breaches aren't caused by AWS failures — they're caused by misconfiguration. Here are 10 concrete best practices to harden your AWS environment in 2026.

AWS Control Tower automates multi-account management — setting up guardrails, enforcing compliance policies, and centralizing billing. This guide covers setup, customization, and production governance patterns.
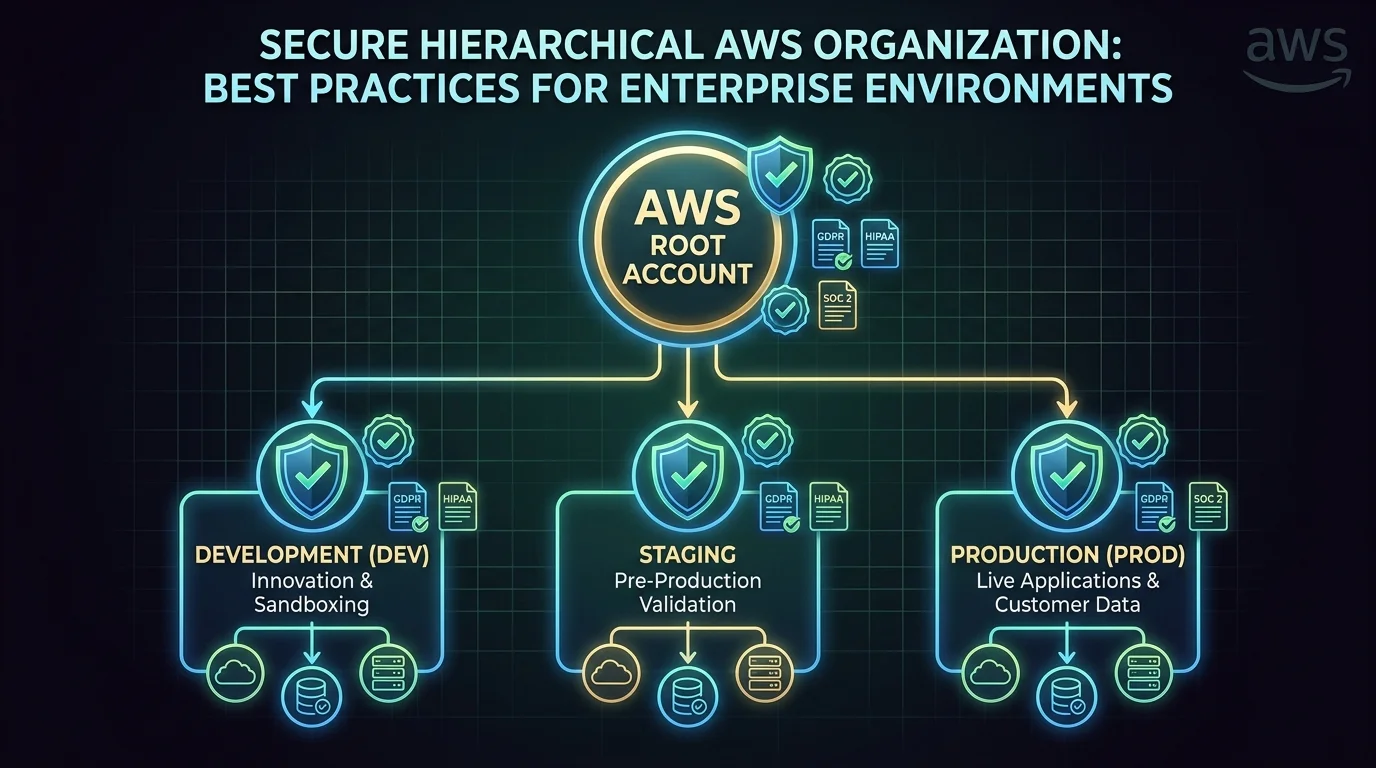
How to structure your AWS organization with multiple accounts for security, compliance, and cost isolation — using AWS Organizations, Control Tower, and a well-designed landing zone.
A practical guide to deploying CloudTrail for production — multi-region trails, KMS encryption, log file integrity validation, organization trails, and CloudTrail Lake as the modern queryable layer for audit, security, and compliance.

A practical guide to the 6 pillars of the AWS Well-Architected Framework and review process — what each pillar covers, why it matters, and how to apply it to your AWS workloads.
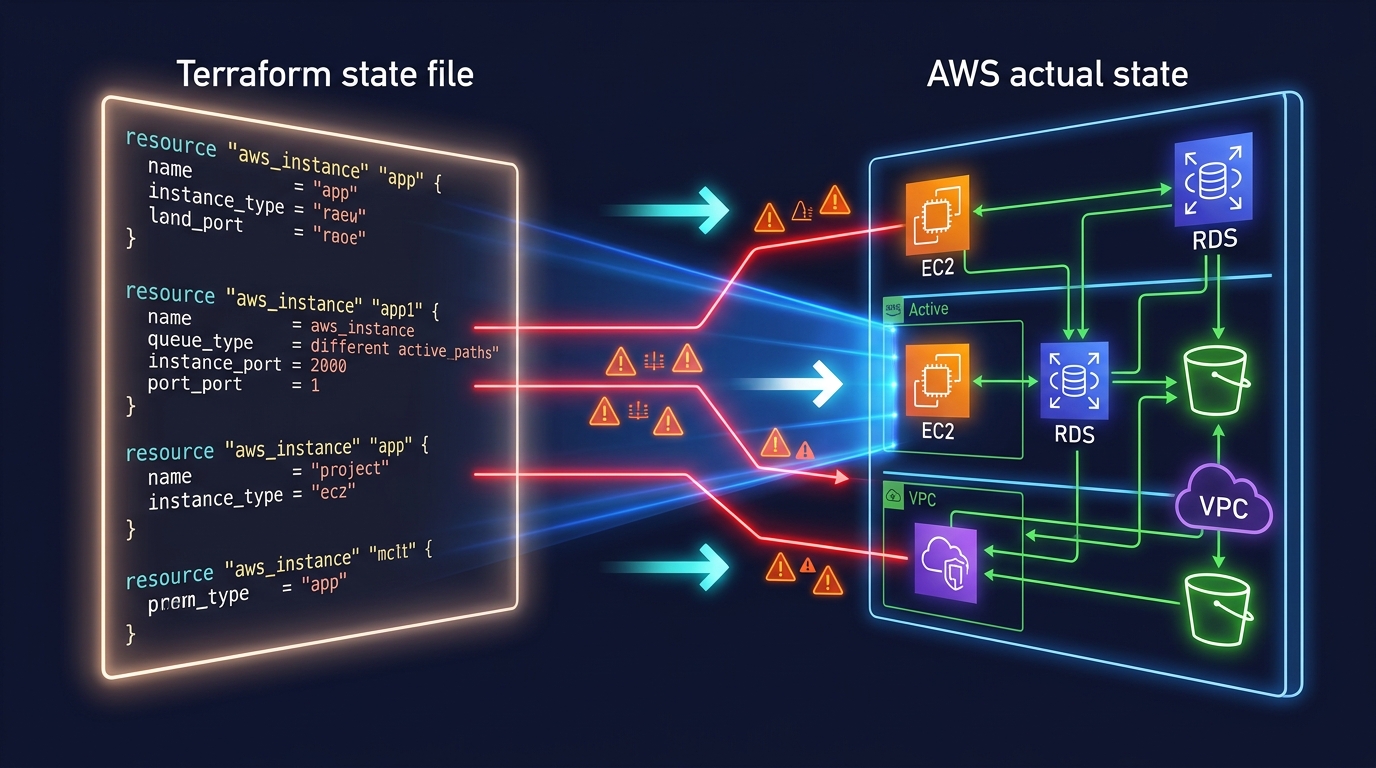
Infrastructure drift—when your actual AWS resources differ from what your IaC declares—causes silent failures and makes disaster recovery impossible. Learn how to detect drift systematically and fix it before it breaks production.
Service-by-service hardening for the AWS resources most often flagged by compliance scanners — DMS replication instances, OpenSearch encryption at rest, SageMaker network isolation, and Lambda runtime end-of-life management.
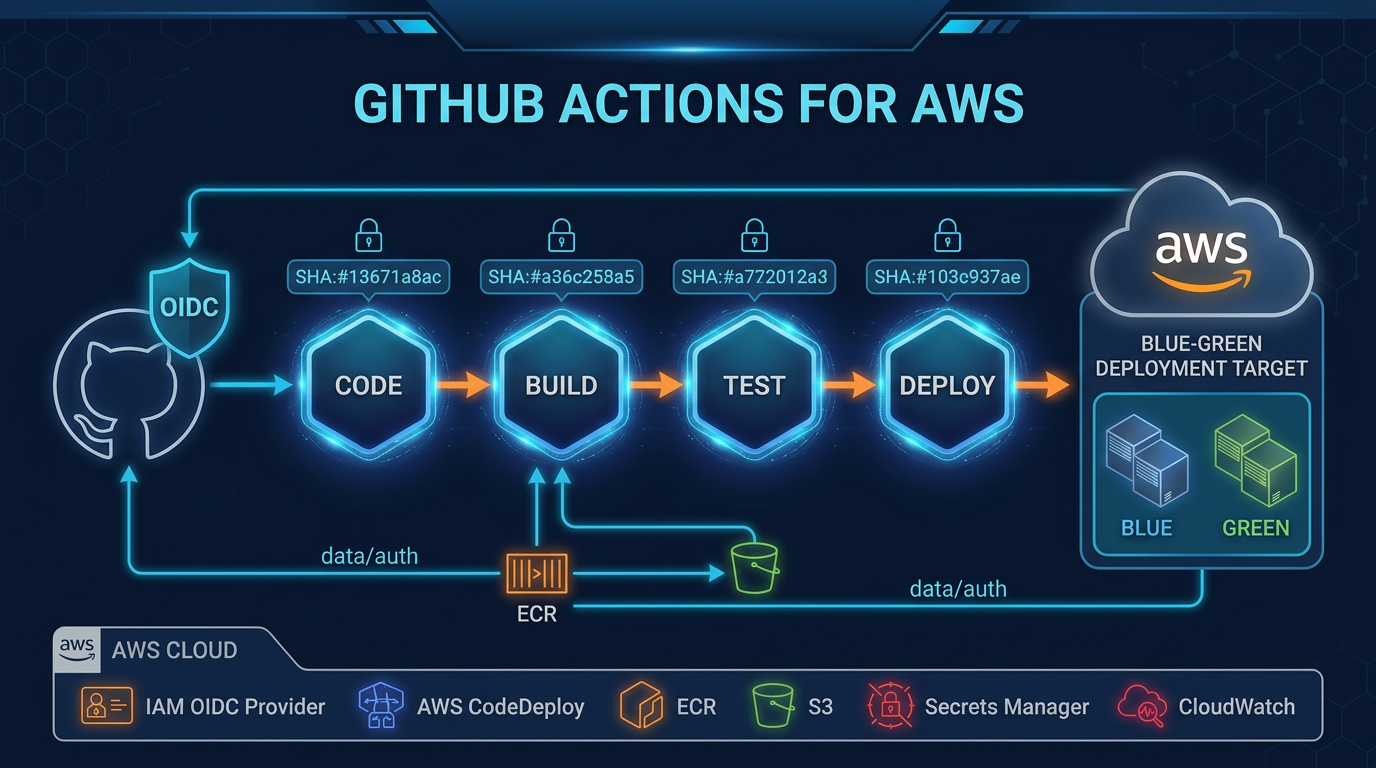
Production-grade GitHub Actions patterns for AWS workloads — OIDC authentication, pinned actions, blue-green deployments, build caching, and the security mistakes that leave your pipeline open to supply chain attacks.
Services
Engagements where we apply the patterns above to your specific environment, regulatory scope, and threat model.
Free AWS Well-Architected Review from FactualMinds. Identify risks, compliance gaps, and optimization opportunities.
Cloud compliance services — HIPAA, SOC 2, PCI DSS, ISO 27001, GDPR. Expert consulting from FactualMinds.
Related subtopics
Sibling subtopics that buyers usually evaluate alongside this one.
Framework-by-framework guidance — what auditors expect, what AWS provides, and what your team configures.
Least-privilege patterns, workforce SSO with identity propagation, customer auth, and fine-grained Cedar-policy authorization.
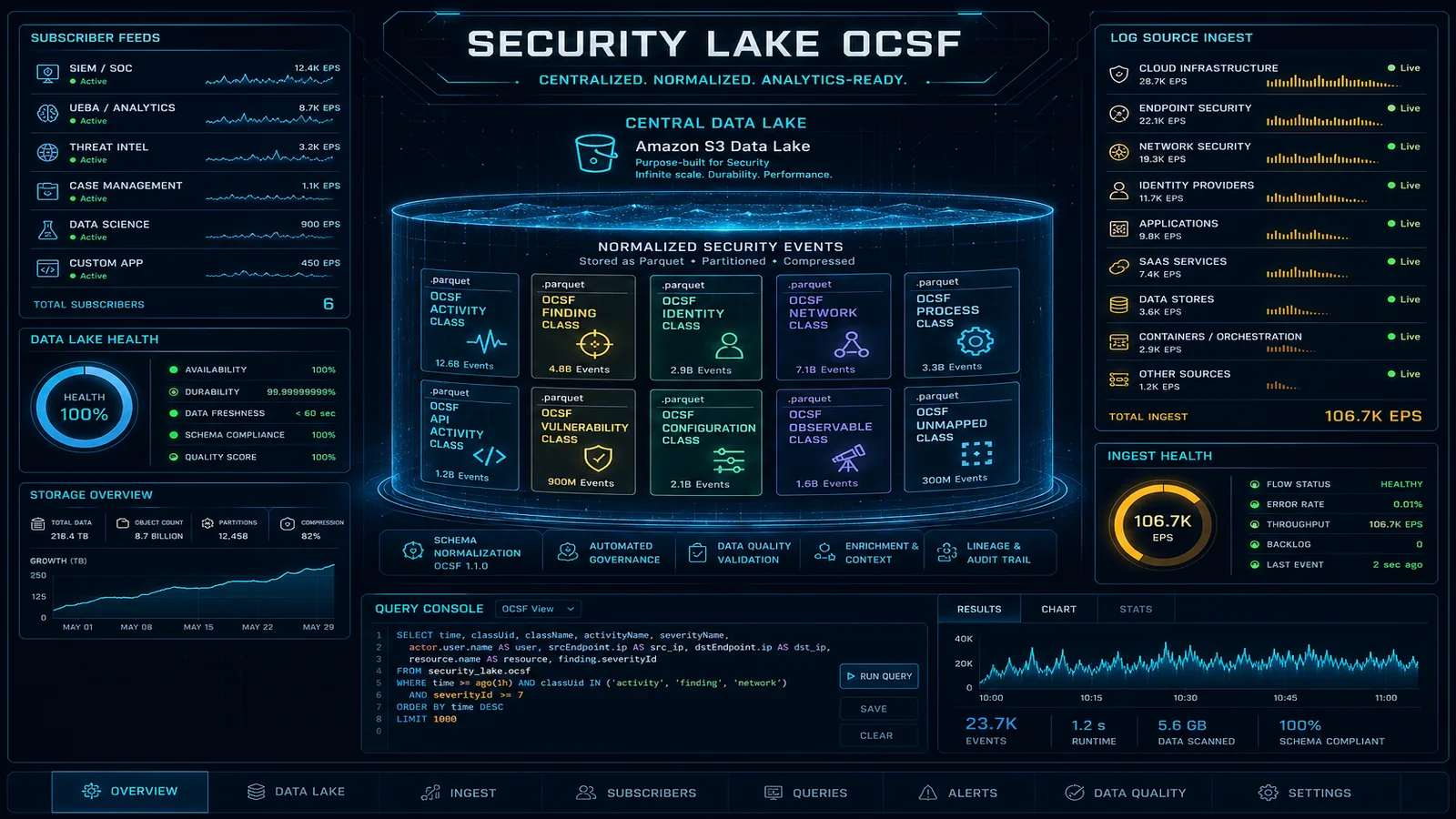
Continuous monitoring, agentless vulnerability scanning, OCSF data lakes, forensic investigation, and automated remediation.
FAQ
Our consulting engagements apply this guidance to your specific environment, regulatory scope, and threat model.
We use cookies and similar technologies to analyze site traffic, personalize content, and provide social media features. By clicking "Accept," you consent to our use of cookies. You can adjust your preferences at any time.