
AWS GuardDuty Threat Detection: A Production Setup Guide
How to deploy, tune, and operationalize Amazon GuardDuty for production threat detection — covering finding types, multi-account setup, automated response, and reducing false positives.
Threat Detection & Response
Continuous monitoring, agentless vulnerability scanning, OCSF data lakes, forensic investigation, and automated remediation.
AWS-native threat detection is enough for most workloads — once it is configured correctly. These guides cover GuardDuty across CloudTrail, VPC, EKS, S3, RDS, Lambda, and EC2 Runtime; Security Hub on its 2025-revised resource-based "Essentials" pricing; Inspector v2 with agentless EC2 (EBS-snapshot scanning), Lambda code scanning, and CI/CD code-repo scanning; Amazon Detective for graph-based forensic investigation across GuardDuty / VPC / CloudTrail; and Security Lake with OCSF 1.1 (1.2 in adoption). Plus the automation that turns findings into remediation runbooks instead of dashboard noise.
Part of the AWS Security & Compliance hub.
Guides

How to deploy, tune, and operationalize Amazon GuardDuty for production threat detection — covering finding types, multi-account setup, automated response, and reducing false positives.

Inspector v2 continuously scans EC2, ECR container images, and Lambda functions without agents. Production guide to CI/CD integration, finding management, risk scoring, and multi-account deployment.
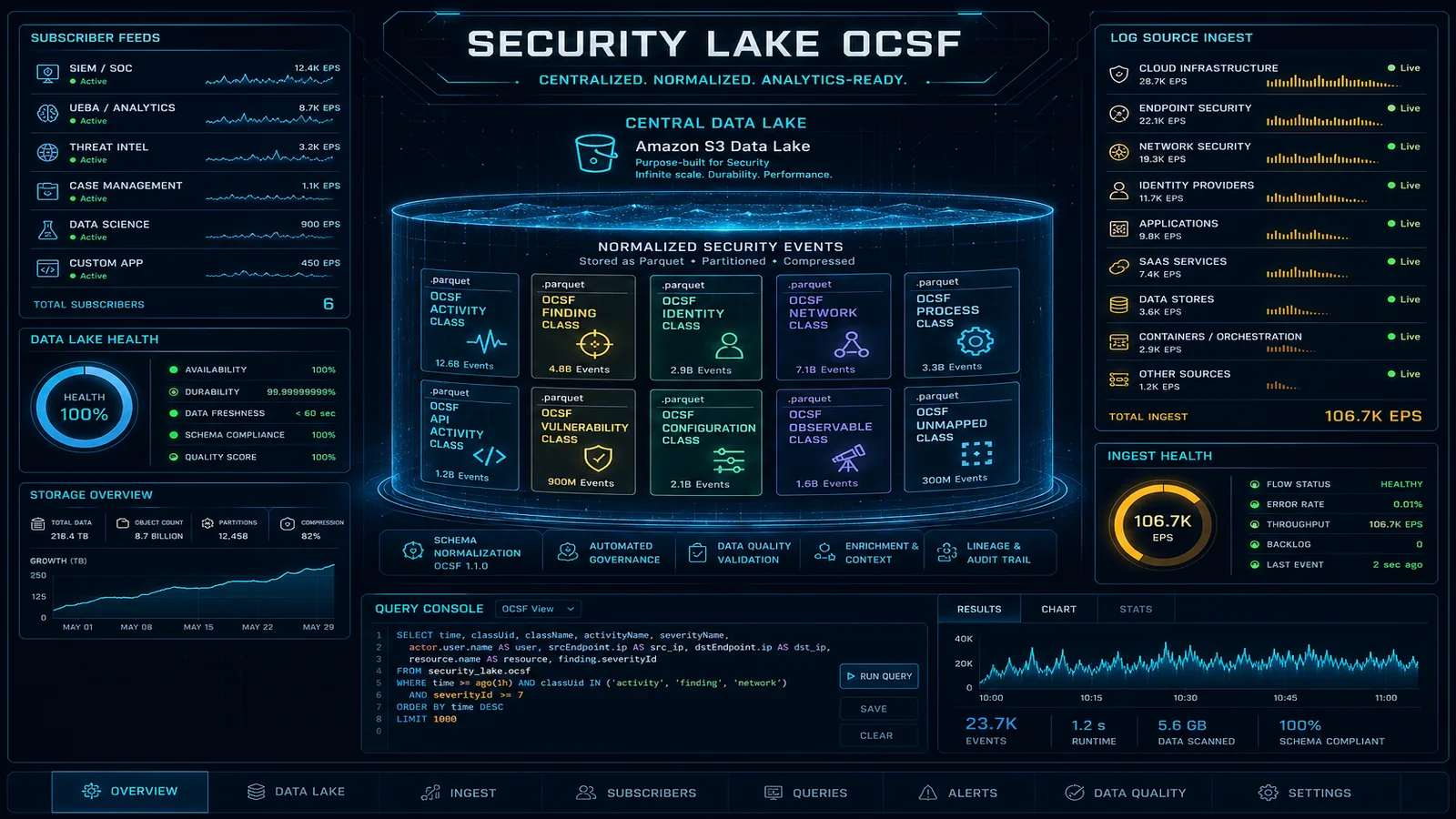
Amazon Security Lake normalizes security logs to OCSF format in a centralized S3 data lake. Here's how to build a cost-effective security data platform without a $500K SIEM contract.
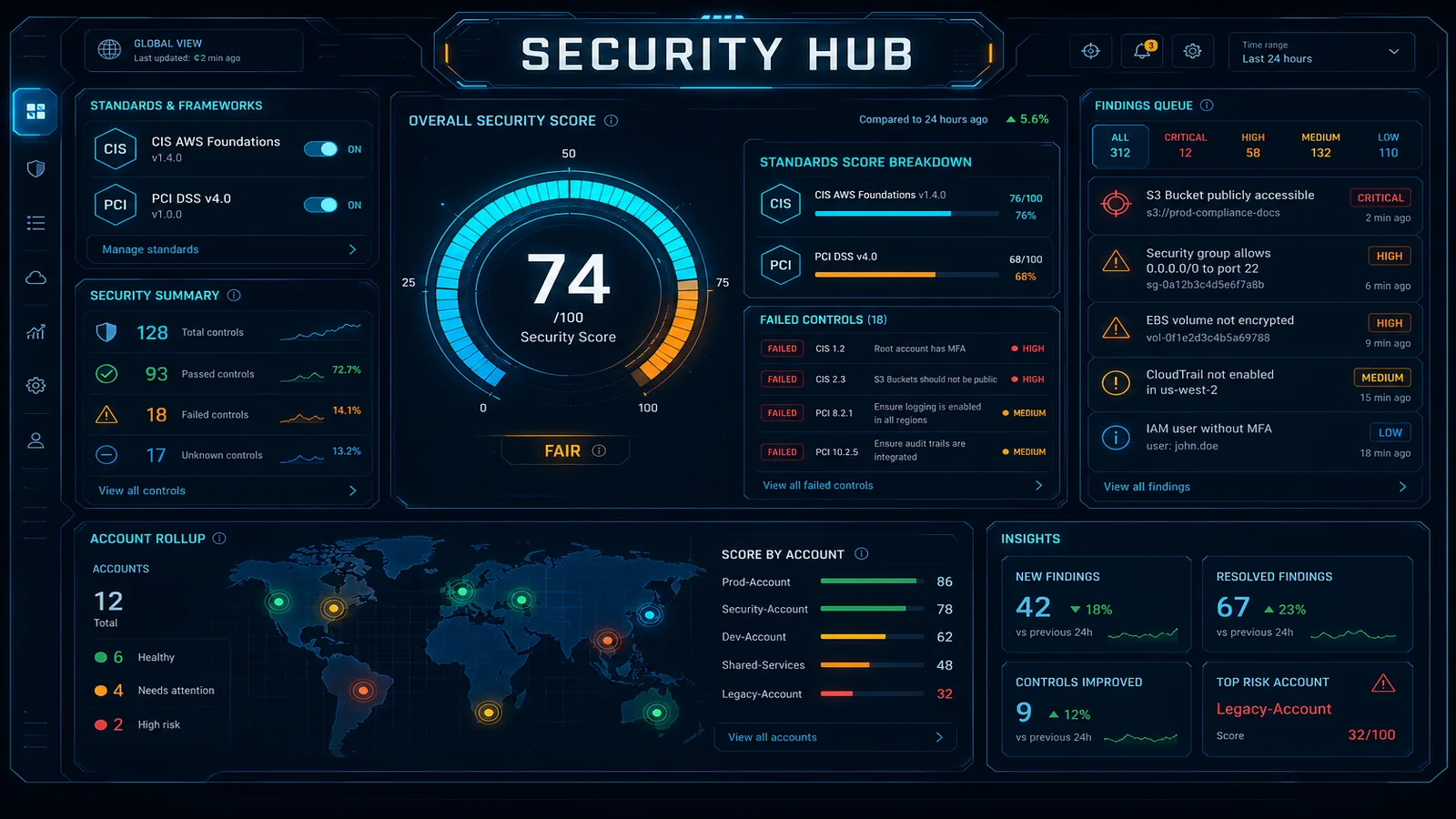
AWS Security Hub aggregates security findings from 200+ sources (GuardDuty, Config, IAM Access Analyzer, Inspector). This guide covers setup, compliance standards (PCI-DSS, CIS, NIST), automated remediation, and building a compliance dashboard without hiring a SOC team.
Manual security triage cannot keep up with cloud-scale threats. Here is how to wire GuardDuty Extended Threat Detection, Security Hub, EventBridge, and Lambda into a self-healing AWS security architecture.
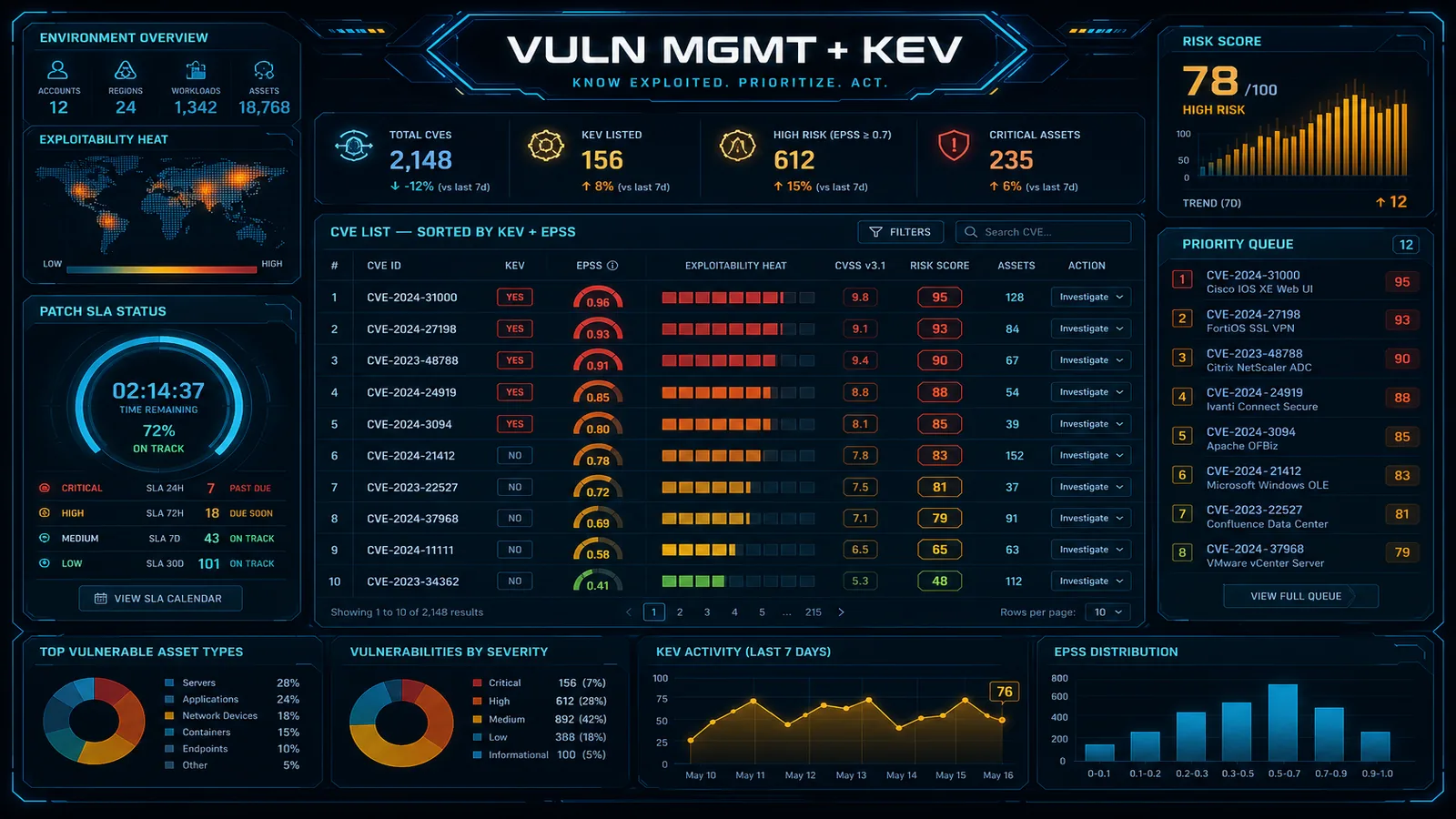
How to build a vulnerability management program that scales beyond CVE-counting. Inspector v2 deployment, CVSS + CISA KEV + reachability for risk-based prioritization, container and IaC scanning in CI/CD, and remediation SLAs that survive audits.

Two AWS-native services that close the gap between "we have S3 buckets and security findings" and "we know where regulated data lives and how a threat moved through our environment." This guide covers production deployment of Macie for data-security posture management and Detective for forensic graph investigation, when each is worth the cost, and how to run them as a paired data-discovery + investigation pipeline.
Services
Engagements where we apply the patterns above to your specific environment, regulatory scope, and threat model.
24/7 managed SOC and MDR for AWS — GuardDuty, Security Hub, Security Lake. Threat hunting, automated containment, incident response from an AWS Select Tier Partner.
AWS security consulting from an AWS Select Tier Partner. 2-week assessment, 4–6 week remediation, zero disruption. IAM hardening, public exposure, compliance gaps, and continuous monitoring.
Related subtopics
Sibling subtopics that buyers usually evaluate alongside this one.
Bucket-level controls, secret rotation, KMS post-quantum, Macie DSPM, and clean-room collaboration without raw-data sharing.
Org-wide guardrails, account isolation strategy, and continuous compliance monitoring as code.
Layer-7 defenses, ZTNA for workforce apps, stateful L3-L7 firewalling, and production-grade VPC patterns.
FAQ
Our consulting engagements apply this guidance to your specific environment, regulatory scope, and threat model.
We use cookies and similar technologies to analyze site traffic, personalize content, and provide social media features. By clicking "Accept," you consent to our use of cookies. You can adjust your preferences at any time.