
AWS S3 Security Best Practices: Preventing Data Exposure
A comprehensive guide to S3 security — bucket policies, encryption, access logging, Block Public Access, and the practices that prevent the data breaches that make headlines.
Data Security
Bucket-level controls, secret rotation, KMS post-quantum, Macie DSPM, and clean-room collaboration without raw-data sharing.
Most "AWS data breaches" are S3 misconfigurations, leaked secrets, or unencrypted analytics joins. The guides below cover bucket-level controls and Block Public Access patterns, secret rotation with Secrets Manager, AWS KMS post-quantum cryptography (ML-KEM hybrid TLS now in KMS, ACM, and Secrets Manager since April 2026; ML-DSA digital signatures GA in KMS), Amazon Macie for PII discovery and DSPM in S3, and privacy-preserving analytics with Clean Rooms.
Part of the AWS Security & Compliance hub.
Guides

A comprehensive guide to S3 security — bucket policies, encryption, access logging, Block Public Access, and the practices that prevent the data breaches that make headlines.
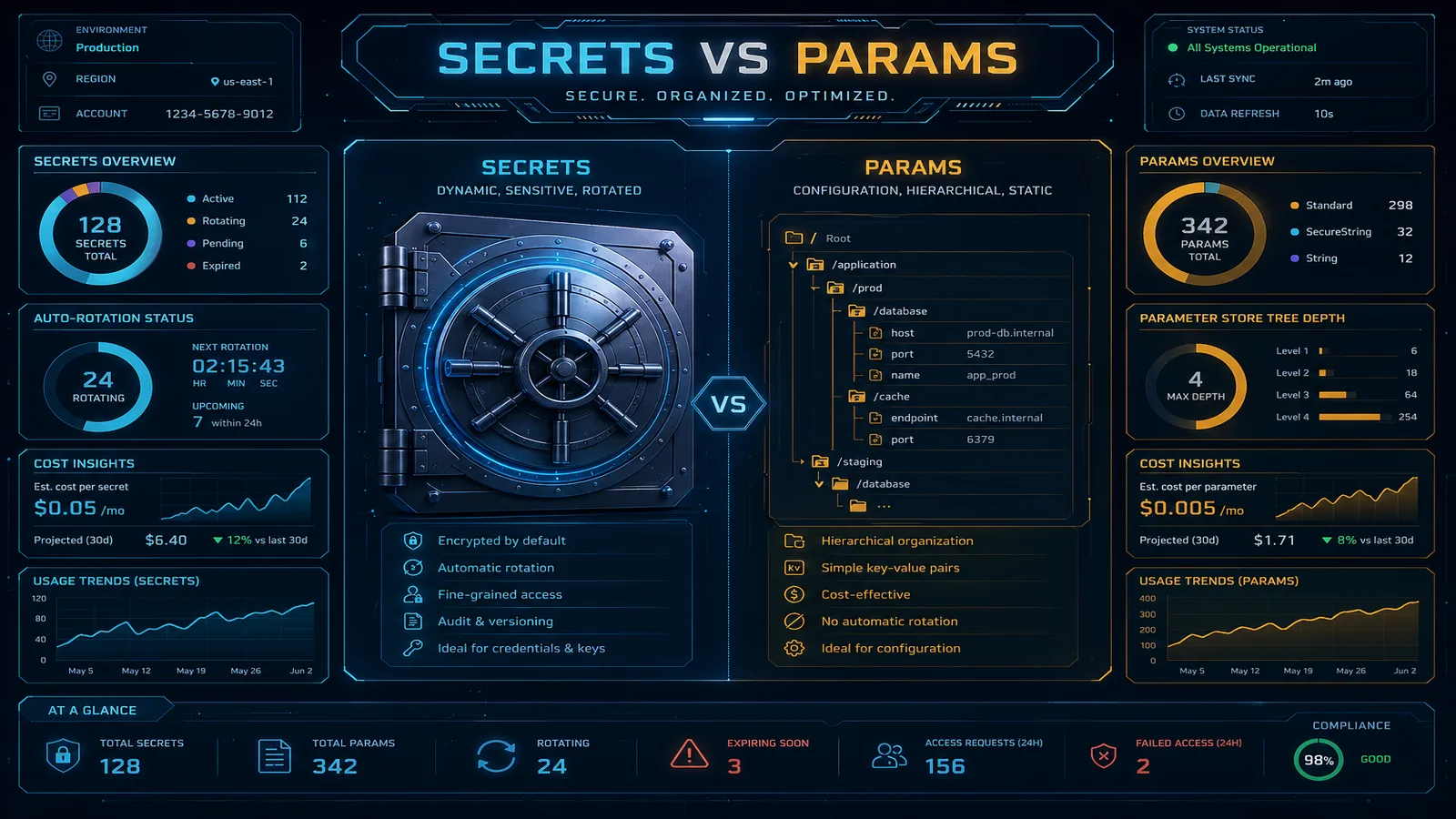
A practical comparison of AWS Secrets Manager and SSM Parameter Store — pricing, rotation, encryption, cross-account access, and clear guidelines for when to use each service for secrets and configuration management.
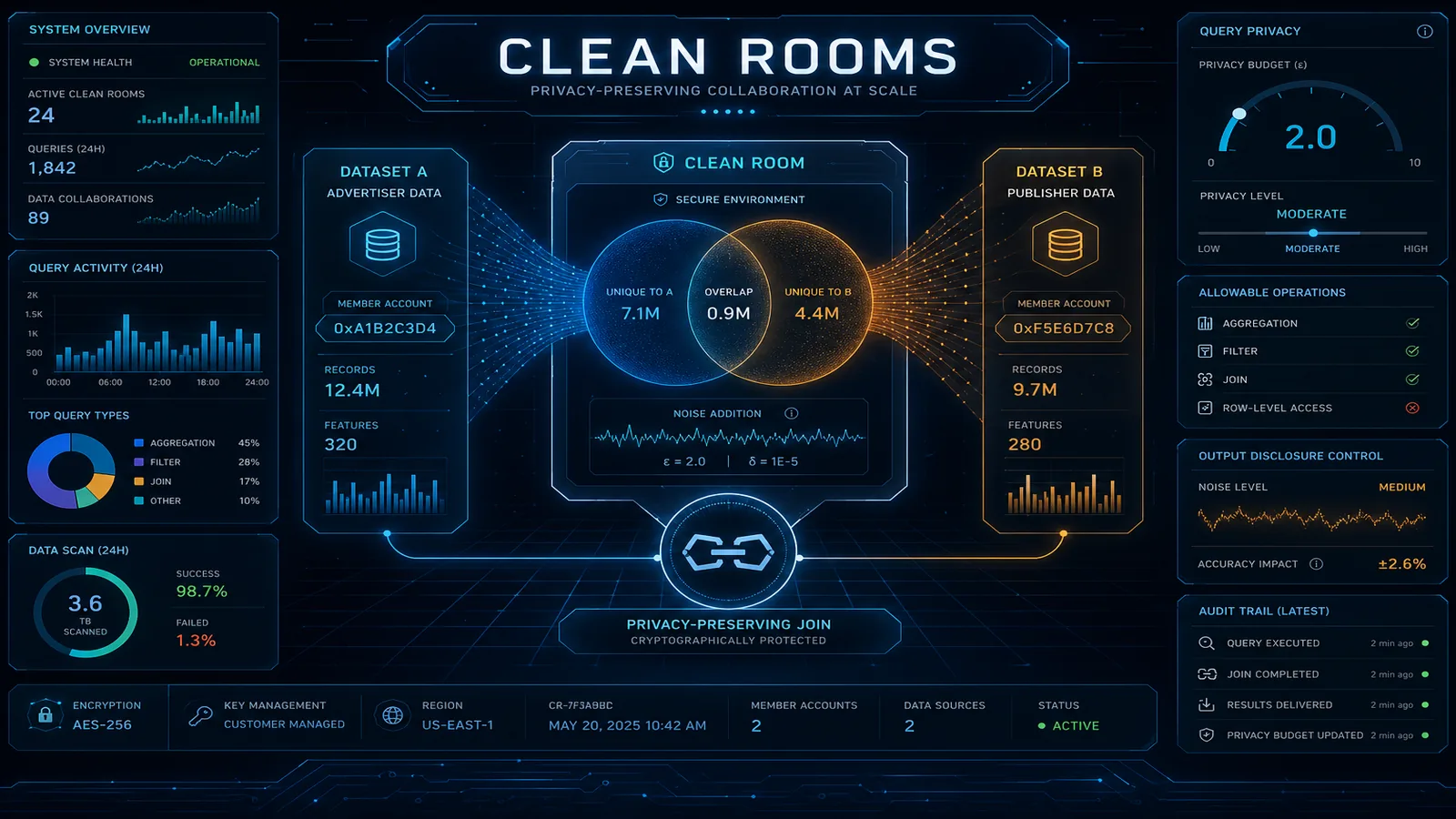
AWS Clean Rooms lets two companies analyze combined data without either seeing the other's raw records. Complete guide to collaboration setup, analysis templates, and compliance evidence for GDPR and SOC 2.

AWS KMS, ACM, and Secrets Manager now support ML-KEM hybrid TLS and ML-DSA digital signatures. This guide covers when to enable post-quantum cryptography, how to configure it across the AWS SDK and TLS clients, performance tradeoffs, and how to plan the migration for long-lived data.

A practical guide to EBS at-rest encryption — account-level default encryption, re-encrypting legacy unencrypted volumes, blocking public snapshots, and operating the KMS key lifecycle without losing data to accidental deletion.

Two AWS-native services that close the gap between "we have S3 buckets and security findings" and "we know where regulated data lives and how a threat moved through our environment." This guide covers production deployment of Macie for data-security posture management and Detective for forensic graph investigation, when each is worth the cost, and how to run them as a paired data-discovery + investigation pipeline.
Services
Engagements where we apply the patterns above to your specific environment, regulatory scope, and threat model.
AWS security consulting from an AWS Select Tier Partner. 2-week assessment, 4–6 week remediation, zero disruption. IAM hardening, public exposure, compliance gaps, and continuous monitoring.
Cloud compliance services — HIPAA, SOC 2, PCI DSS, ISO 27001, GDPR. Expert consulting from FactualMinds.
Related subtopics
Sibling subtopics that buyers usually evaluate alongside this one.
Continuous monitoring, agentless vulnerability scanning, OCSF data lakes, forensic investigation, and automated remediation.
Framework-by-framework guidance — what auditors expect, what AWS provides, and what your team configures.
AI-specific risk: prompt injection, PII leakage, hallucinations, and compliant model deployment for regulated industries.
FAQ
Our consulting engagements apply this guidance to your specific environment, regulatory scope, and threat model.
We use cookies and similar technologies to analyze site traffic, personalize content, and provide social media features. By clicking "Accept," you consent to our use of cookies. You can adjust your preferences at any time.