AWS Security Agent Full Repository Code Review: Trust Boundaries Beyond Pattern-Only SAST
Quick summary: On May 12, 2026 AWS announced full repository code review for AWS Security Agent—whole-codebase reasoning over trust boundaries and data flows plus file/line remediations, preview at no additional charge for existing Security Agent customers.
Key Takeaways
- AWS states that findings can ship with remediation tied to concrete files and lines, aimed at shortening the path from detection to mergeable fix
- Always confirm current terms in official AWS pages before enabling in production accounts
- Reproduce this — Pilot checklist: What Is AWS Security Agent Full Repository Code Review
- Capability and preview terms trace to AWS What's New — May 12, 2026; current console behavior lives on AWS Security Agent
- Why whole-repository reasoning matters Most static analysis products excel at local pattern checks: a dangerous API call, a weak crypto import, a SQL string built with concatenation

Table of Contents
On May 12, 2026, AWS announced full repository code review for AWS Security Agent: a capability that analyzes an entire codebase with an emphasis on architecture, trust boundaries, and data flows, not only matching lines against vulnerability templates. AWS states that findings can ship with remediation tied to concrete files and lines, aimed at shortening the path from detection to mergeable fix.
This post is not a feature announcement rewritten as marketing fluff. It is a field-ready placement guide: how repo-wide agentic analysis fits beside the controls we already recommend for AWS teams—Inspector for CVE-style exposure, **vulnerability-management discipline** for prioritization, and **CI/CD AppSec** plus **secure GitHub Actions** for delivery gates.
AWS notes the capability ships in Regions where AWS Security Agent is offered, at no additional charge for existing AWS Security Agent customers during the preview, and directs readers to the AWS Security Agent console and documentation. Always confirm current terms in official AWS pages before enabling in production accounts.
Reproduce this — Pilot checklist:
examples/architecture-blog-2026/security-agent/full-repo-review-pilot.md
What Is AWS Security Agent Full Repository Code Review?
AWS describes full repository code review as deep, repository-wide security analysis: reasoning across architecture, trust boundaries, and data flows, not merely matching snippets to known insecure patterns. When it reports issues, it can attach developer-oriented remediation tied to concrete files and lines—think systemic design flaws surfaced with a plausible fix path rather than isolated lint hits. Capability and preview terms trace to AWS What’s New — May 12, 2026; current console behavior lives on AWS Security Agent.
Why whole-repository reasoning matters
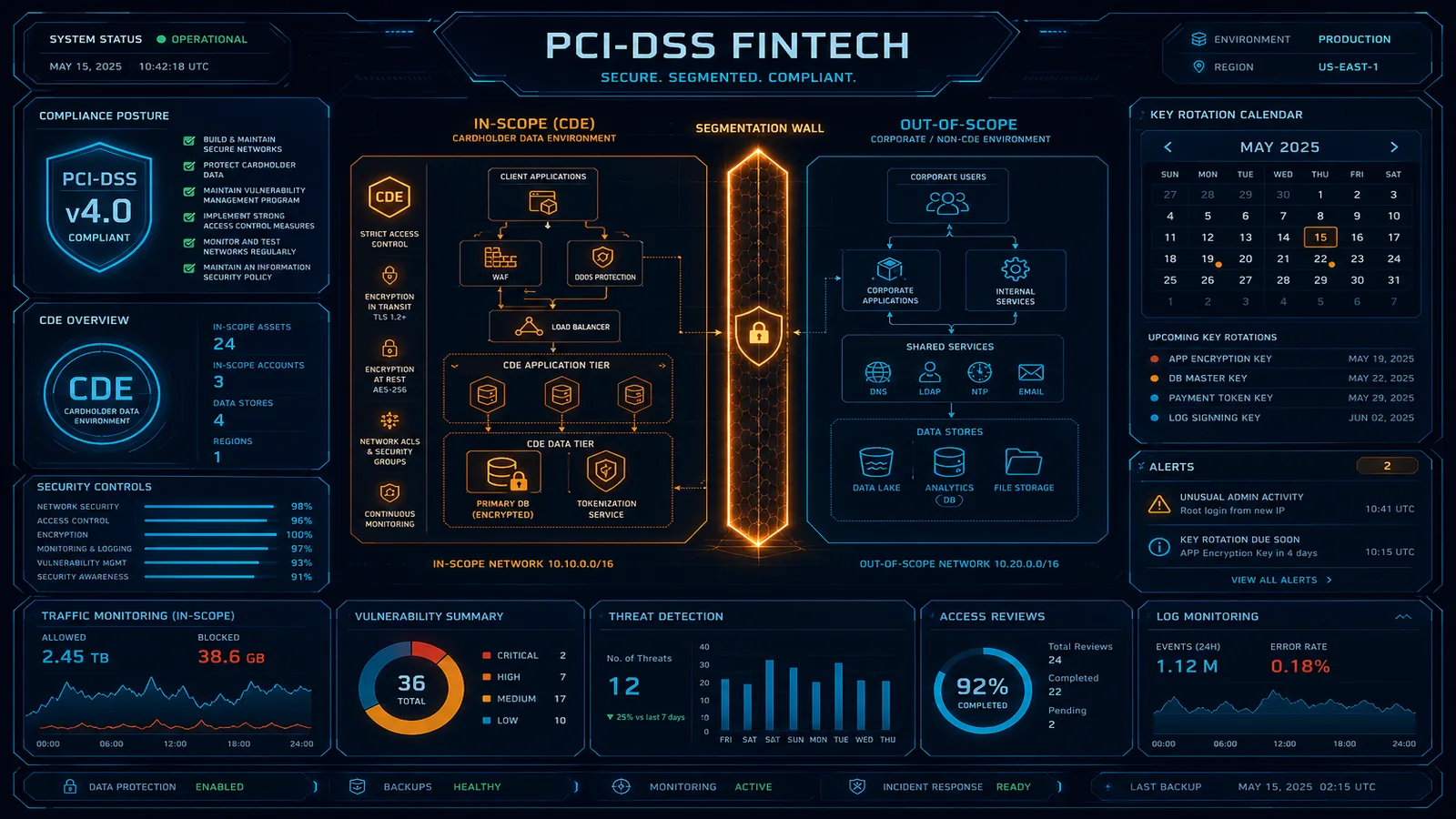
Most static analysis products excel at local pattern checks: a dangerous API call, a weak crypto import, a SQL string built with concatenation. Those checks matter. They also systematically miss failures that only appear when modules agree on the wrong trust model—when an “internal” queue consumer assumes every message is pre-authorized, when a shared DTO crosses a boundary that should have been validated twice, or when two services disagree on who may mint a session token.
Announced behavior for full repository code review is explicitly context-aware across the tree: AWS describes reasoning about application architecture and data flows, not only signature hits. That is the right axis to complement—not replace—your existing workload hardening and security hygiene baselines.
What “full repository” changes in how teams work
A repository is not a bag of files; it is a graph of dependencies, configuration, and runtime contracts. When analysis spans that graph, three operational shifts land on engineering leads:
- Triage becomes architectural — Findings may implicate multiple packages or services. Your IAM least-privilege baselines and service ownership map need to be current so tickets land on the right team.
- Remediation is diff-shaped — File/line fix suggestions shorten implementation time when paired with disciplined code review—the same skepticism applied to Amazon Q Developer–style workflows should apply here.
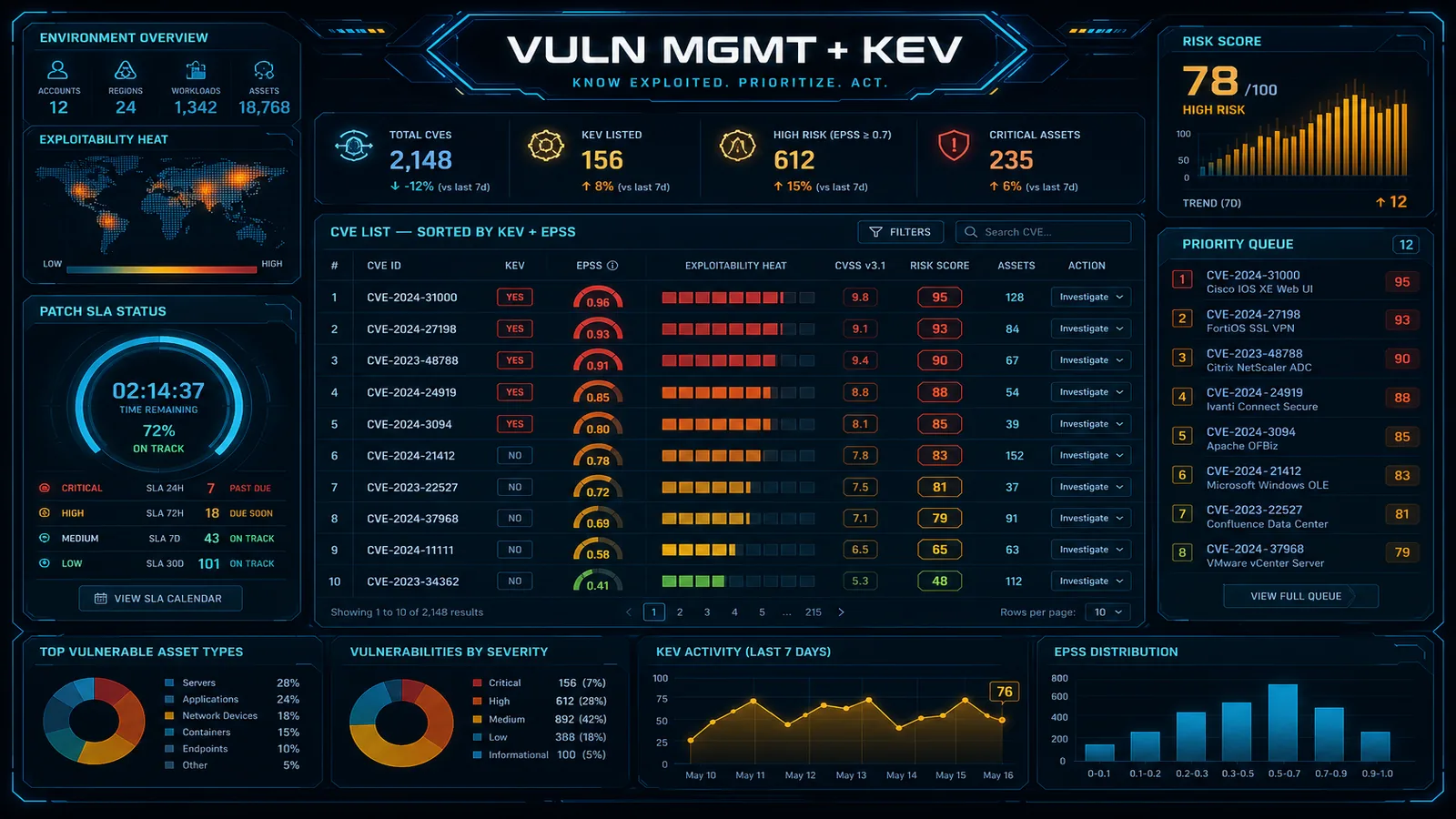
- Evidence joins the VM program — Push systemic issues into your CVSS / KEV / reachability workflow so Severity-10 dependency noise does not drown Severity-Right logic flaws.
Pilot with one bounded codebase (bounded path or service slice). Expand only after Security Hub aggregation and ownership models prove they scale with novelty.
Portfolio map on AWS — where Security Agent sits
| Capability | Primary signal | Typical best for |
|---|---|---|
| Amazon Inspector v2 | Packages, CVEs, Lambda/package inventory, enhanced container scanning (guide) | Supply-chain CVE closure, continual re-scan on new vulns |
| CodeGuru Security, OSS advisories, CI SAST (VM, pipelines) | Rules on changed surfaces, dependency advisories | Fast regressions before merge |
| AWS Security Agent — full repo review (announcement 2026-05-12) | Cross-module architecture, flows, remediation hints per AWS | Systemic misuse of trust boundaries, dangerous end-to-end paths |
Opinionated take: If you only mature one layer this quarter, finish Inspector + dependency gates first—unpatched CVEs are measurable and auditable. Add full-repo reasoning once those layers are staffed for triage, so new findings amplify engineering judgment instead of replacing it.
Operational integration patterns
Use these patterns together on AWS-heavy applications:
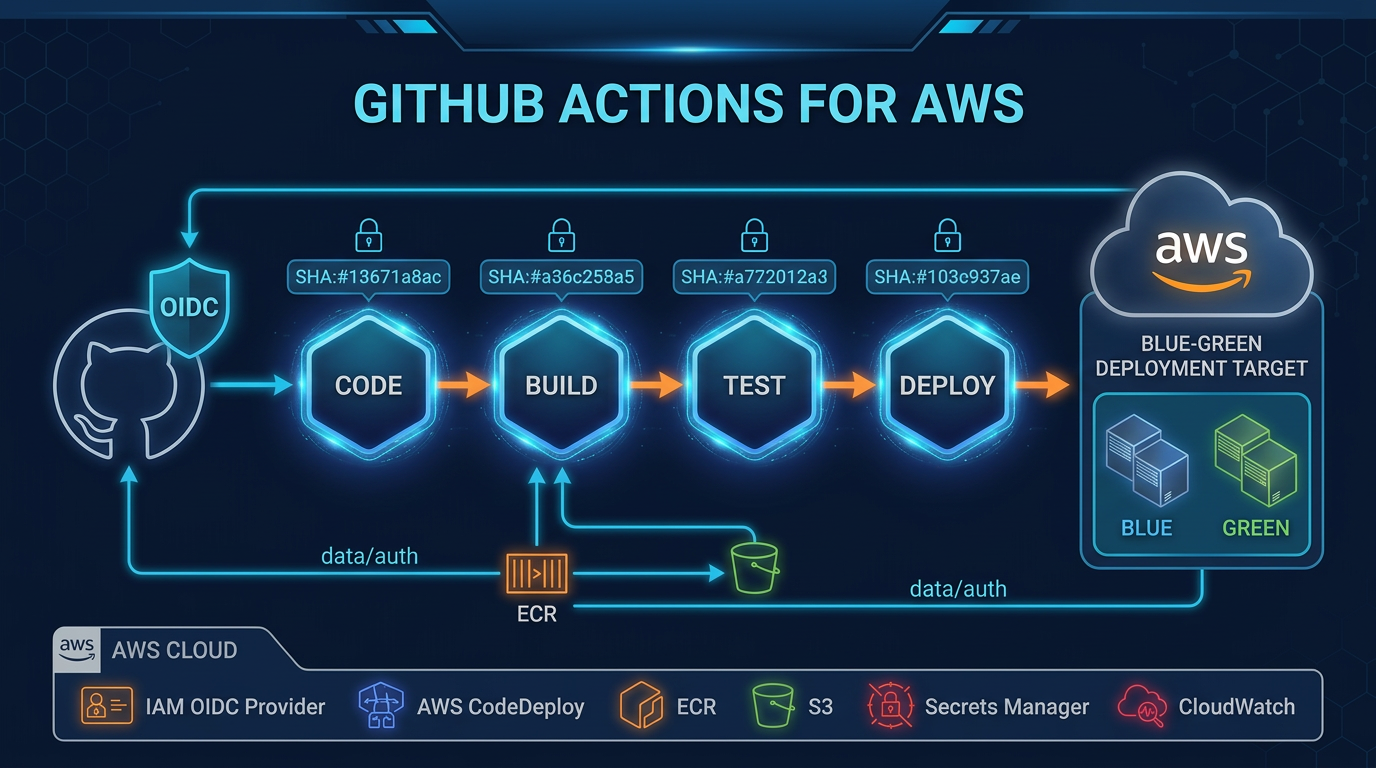
- GitHub Actions with OIDC to AWS IAM — Keep long-lived secrets out of CI; scanners should not incentivize pasted keys.
- Security Hub as posture hub — Route confirmed misconfigurations and policy failures into dashboards your executives already read.
- GuardDuty for runtime narratives — Code review lowers defect rate; WAF protections and WAF production patterns constrain how defects express in prod (where allowed).
- Proactive remediation runbooks — Turn repeated systemic classes into parameterized fixes and guardrails instead of infinite one-off patches.
AWS’s What’s New commentary also observes that modern AI-assisted security tooling can accelerate both finding and exploit exploration industry-wide—which is precisely why defenders should prioritize narrow blast radius, immutable deploy artifacts, Well-Architected security literacy, and continuous validation—not fear-mongering, but risk-aware engineering.
Where sensitive data classifications matter, Macie investigations and detective workflows still guard stored exposures; reviewer comments should respect classification boundaries when filing tickets publicly.
Risk register for agentic code review adoption
Teams fail this class of rollout for predictable reasons:
Alert bankruptcy — No owner, SLA, or rubric converts “novel signal” into “ignored backlog.” Borrow from nist-csf-2 posture rhythms: Identify, Protect, Detect, Respond, Recover—all need names next to checkbox items for new tooling.
Over-trusting machine-written patches — The worst failure is merging a plausible diff that subtly widens IAM trusts or network egress. Require human review anchored in architecture review practices and staged rollout.
Confidential code paths — If your pilot repository includes contractual “do not automate” carve-outs, carve them out mechanically (path filters, repos, or forks) rather than verbally.
AWS positions preview access for existing customers specifically to deepen collective defender learning. Treat your pilot as contributing to internal playbooks—not a secret magic shield.
When to pull in consulting help
If full-repo scanning surfaces cross-account trust refactors outside your roadmap, AWS Cloud Security engagements and pipeline modernization can pair policy work with IaC remediation so fixes stay mergeable—not slide-deck-only narratives.
What This Post Doesn’t Cover
Exact IAM privileges, data-plane paths, or retention semantics inside AWS Security Agent—those belong in official AWS Security Agent product and documentation pages linked from What’s New.
Step-by-step console click paths beyond “enable via Security Agent console” as stated by AWS; UI flows change frequently.
Benchmark numbers comparing this capability to external SAST vendors—organizations should measure internally against their own codebase shape and SLA.
If You Only Do One Thing
Run a single bounded pilot with a written severity rubric, explicit triage owners, and a fourteen-day SLA before enabling org-wide rollout.
What to Do This Week
- Confirm Legal / procurement clears repo-scale analysis for the pilot codebase.
- Align engineering + security leads using the linked worksheet checklist (
full-repo-review-pilot.md). - Reconcile IAM and network trust boundaries surfaced by any systemic finding with IAM best practices and Security Hub reporting conventions.
AWS Cloud Architect & AI Expert
AWS-certified cloud architect and AI expert with deep expertise in cloud migrations, cost optimization, and generative AI on AWS.