CI/CD Threat Models and Web App Security on AWS: Pipelines, XSS, CSRF, and SQL Injection
Quick summary: GitHub Actions OIDC role sessions are short-lived by design—teams still paste static access keys into workflow logs until scanners or audits catch the diff; supply-chain writeups keep repeating the pattern into 2026.
Key Takeaways
- On May 8, 2026, the dominant CI/CD compromise class is still “credential sprawl meets YAML
- The fix AWS partners preach—OIDC federation from GitHub Actions to IAM without long-lived keys—is documented end-to-end in our flagship GitHub Actions secure CI/CD guide
- This article does not duplicate that playbook; it gives the threat model spine and maps OWASP-style failures (XSS, CSRF, SQLi) to AWS controls
- Opinionated take — If production deploy still requires an IAM user access key, file a P0 debt ticket—there are few excuses left after OIDC maturity
- For internet-facing HTTP, pair code review with AWS WAF production guidance and API abuse protections
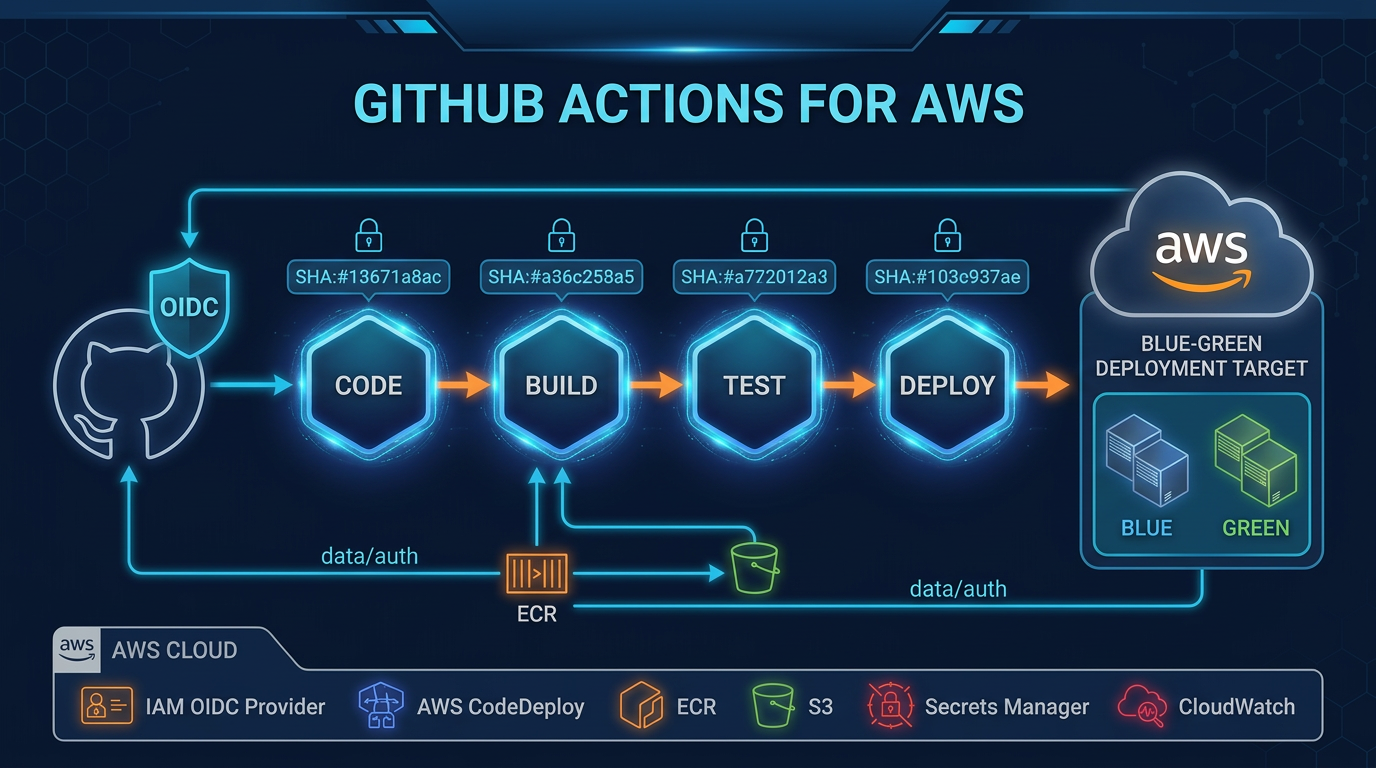
Table of Contents
On May 8, 2026, the dominant CI/CD compromise class is still “credential sprawl meets YAML.” The fix AWS partners preach—OIDC federation from GitHub Actions to IAM without long-lived keys—is documented end-to-end in our flagship GitHub Actions secure CI/CD guide. This article does not duplicate that playbook; it gives the threat model spine and maps OWASP-style failures (XSS, CSRF, SQLi) to AWS controls.
Reproduce this — Pipeline gate worksheet:
examples/architecture-blog-2026/cicd-appsec/pipeline-control-gates.md
CI/CD threat surface (compressed)
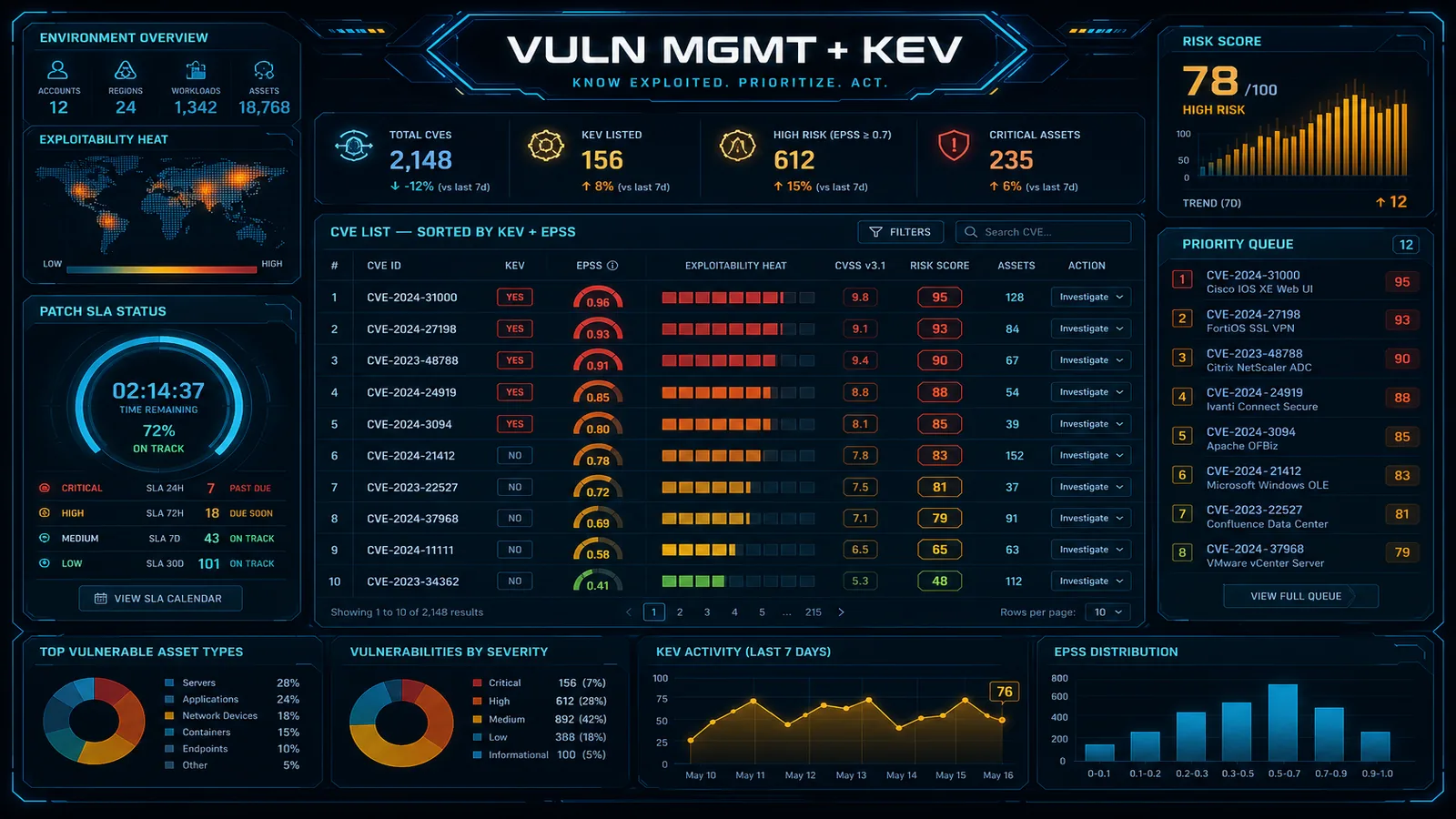
| Threat | Typical failure | AWS-aligned control |
|---|---|---|
| Stolen build secrets | Keys in logs, world-writable buckets | OIDC roles, KMS CMKs, deny policies on public artifacts |
| Malicious PR | Untrusted pull_request_target | Branch protections, CODEOWNERS, ephemeral runners |
| Compromised third-party action | Tag drift / supply chain | SHA pinning, private mirrors |
| Drift between prod/staging | Config-only “hotfix” | Same IaC modules, promotion gates |
Deep procedures: follow the long-form GitHub Actions article; operational checklist lives in the worksheet above.
Opinionated take — If production deploy still requires an IAM user access key, file a P0 debt ticket—there are few excuses left after OIDC maturity.
XSS: defense in layers
Encoding output beats fancy WAF regexes. For internet-facing HTTP, pair code review with AWS WAF production guidance and API abuse protections.
Failure mode: admin consoles trusting rich text stored in RDS without sanitization—WAF cannot see server-side stored XSS rendering inside authenticated sessions.
CSRF: follow your session model
Cookie sessions need CSRF tokens / SameSite discipline. Bearer tokens in memory change risk posture but introduce other XSS blast radius problems—pick intentionally.
SQL injection: RDS is not magical
Use parameterized queries everywhere raw SQL appears. For ORM users: ban string-built WHERE clauses.
Pair database hygiene with broader hardening in 10 AWS security practices and beyond-the-basics workload security.
What broke — A reporting microservice built
ORDER BY ${userColumn}for “flexibility.” Automated scanners missed it until a tenant passedid; DROP TABLEscaffolding in staging. Fix: allow-list sort columns, separate reporting replica with read-only creds.
What This Post Doesn’t Cover
- Container image signing deep dive (refer to Inspector + CI guide cross-links in the GitHub Actions article).
- IAM Permission Boundaries math for deployment roles—covered better in IAM best practices.
If You Only Do One Thing
Turn on organization-level OIDC patterns and delete the last AWS_ACCESS_KEY_ID secret used for deployment—measure blast radius reduction in quarterly access reviews.
What to Do This Week
- Walk the pipeline worksheet with security + platform leads; assign owners per unchecked row.
- Run SAST + dependency scan on default branch; block promotion on criticals without risk acceptance record.
- Spot-check top 10 dynamic SQL calls for interpolation—ORMs hide surprises.
Continue architecture resilience reading at production resilience patterns and data coupling at distributed data field notes.
AWS Cloud Architect & AI Expert
AWS-certified cloud architect and AI expert with deep expertise in cloud migrations, cost optimization, and generative AI on AWS.