· Palaniappan P · 2 min read
CI/CD Threat Models and Web App Security on AWS: Pipelines, XSS, CSRF, and SQL Injection
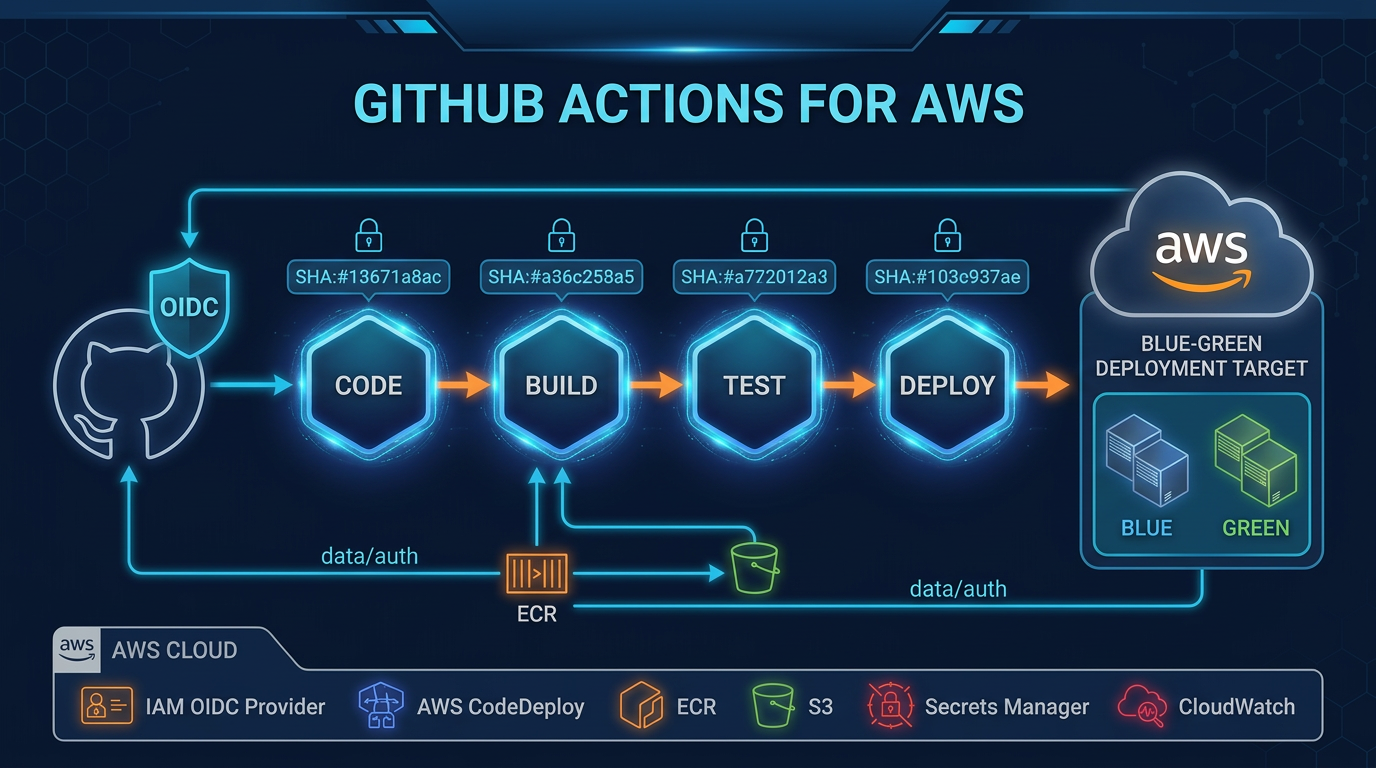
GitHub Actions OIDC role sessions are short-lived by design—teams still paste static access keys into workflow logs until scanners or audits catch the diff; supply-chain writeups keep repeating the pattern into 2026.
