AWS MCP Server Hits GA: What It Changes for Agentic Development (Plus the Serverless Agent Plugin)
Quick summary: On May 6, 2026, AWS made its managed MCP server generally available in 2 regions—with IAM guardrails, CloudWatch metrics, and CloudTrail logging—while the March 25, 2026 Agent Plugin for AWS Serverless brought packaged SAM/CDK skills into Cursor and Claude Code.
Key Takeaways
- The shift in one sentence Agents stop being a productivity hack and start being a software supply-chain channel the moment they can mutate infrastructure
- GA hardening (IAM boundaries + CloudTrail + metrics) is AWS acknowledging that reality for enterprise buyers
- What GA added beyond preview (and why practitioners notice) AWS positions the MCP Server as part of the broader Agent Toolkit for AWS
- Sandboxed script execution so agents can run Python against AWS for multi-step work without your local filesystem/shell becoming the trust boundary for every contractor
- Operational visibility: CloudWatch metrics plus CloudTrail logging—i

Table of Contents
On May 6, 2026, AWS announced general availability of the AWS MCP Server—a managed Model Context Protocol surface that lets AI coding agents call AWS APIs with IAM-based guardrails, Amazon CloudWatch metrics, and AWS CloudTrail logging. That same week, teams already experimenting with Cursor, Claude Code, and Kiro had another reason to treat “agent access to cloud” as a platform decision—not a personal API key taped to a developer laptop.
Two months earlier, on March 25, 2026, AWS shipped a complementary piece: the Agent Plugin for AWS Serverless, which packages skills, sub-agents, hooks, and MCP servers into one installable unit aimed at serverless delivery (Lambda, events, SAM/CDK, API Gateway, durable workflows).
This post connects those announcements, names the trade-offs we actually see in platform reviews, and gives you a Monday-morning checklist—without pretending a single architecture fits every regulated tenant.
The shift in one sentence
Agents stop being a productivity hack and start being a software supply-chain channel the moment they can mutate infrastructure. GA hardening (IAM boundaries + CloudTrail + metrics) is AWS acknowledging that reality for enterprise buyers.
What GA added beyond preview (and why practitioners notice)
AWS positions the MCP Server as part of the broader Agent Toolkit for AWS. Since the re:Invent 2025 preview, the GA post highlights capabilities that matter in security reviews:
- One tool path to AWS APIs, including operations that need file uploads or long-running behavior—reducing bespoke “agent script of the week” sprawl.
- Sandboxed script execution so agents can run Python against AWS for multi-step work without your local filesystem/shell becoming the trust boundary for every contractor.
- Agent skills as a structured replacement for brittle “agent SOPs” text dumps—curated procedures that agents load on demand, which helps both quality and context-window discipline.
- Documentation search and skill discovery without AWS credentials, which removes a common onboarding blocker for learning paths (distinct from executing privileged API calls—those still require real authn/authz).
- Operational visibility: CloudWatch metrics plus CloudTrail logging—i.e., answers to “which principal invoked what, when, from which agent session?”
Quantified scope note (from AWS, not a customer claim): at GA, AWS documents 2 opt-in Regions for the managed MCP Server: US East (N. Virginia) and Europe (Frankfurt). Plan capacity and data residency accordingly.
Commercial framing (also from AWS): the MCP Server itself is no additional charge; you pay for AWS resources consumed by the workflows your agents trigger. Cost governance shifts from “seat licenses” to API blast radius.
The March 2026 Serverless Agent Plugin—what it is, what it is not
The March 25, 2026 announcement is explicitly about how agents build and operate serverless systems, not about generic “cloud guidance.” AWS calls out:
- Lambda with common event sources (Amazon EventBridge, Amazon Kinesis, AWS Step Functions).
- AWS Serverless Application Model (SAM) and AWS CDK patterns—constructs, CI/CD templates, local testing flows.
- Lambda durable functions patterns (checkpoint/replay mental model, orchestration, error handling).
- Amazon API Gateway coverage across REST, HTTP, and WebSocket APIs.
The plugin exposes capabilities as Agent Skills in the open Agent Skills format so compatible tools can load them consistently.
Install pointers (verify before you paste—marketplaces change fast):
- Claude Code users can install from the Claude Marketplace AWS Serverless plugin page using the documented
/plugin installflow referenced in the announcement. - The
awslabs/agent-pluginsGitHub repository is the public home for exploration beyond marketing copy.
What it is not: a substitute for your threat model. A skill can be excellent and still suggest a change that violates your organizational policy. Policy-as-code, human review, and environment separation remain on you.
How we think about pairing MCP GA with the Serverless plugin (opinionated)
Recommendation: treat AWS MCP Server (GA) as the control plane for “agents touching AWS APIs”, and the Serverless Agent Plugin as the delivery acceleration layer for “serverless code + IaC + local validation.”
- Choose managed MCP Server + tight IAM roles when auditability and scalable onboarding matter more than absolute minimal latency for a solo developer.
- Choose plugin-first iteration when your bottleneck is repeatable SAM/CDK structure, test harnesses, and API Gateway semantics—not raw API reach.
Trade-off stated plainly: centralized MCP routes add process win (logging, guardrails, discovery), but region availability and cross-account patterns can add architecture work. If your org cannot justify that overhead yet, pilot in one dev account with break-glass procedures before expanding.
Failure modes that still happen after GA
What breaks in real rollouts — Teams grant an overly wide “agent role” to reduce friction, then an agent removes the wrong resource guardrail or opens a security group while trying to “fix” a failing deploy. CloudTrail gives you the forensics, but it does not replace preventive guardrails (SCPs, permission boundaries, explicit denies, review gates). Detection without prevention is an incident report, not a strategy.
Counter-case — If your developers only need read-only metadata (describe/list) and you already have short-lived SSO-based credentials with session policies, a minimal local tool may be faster to pilot. The GA MCP Server’s wins accumulate when multiple teams, contractors, and automation accounts share the same pattern.
Reproduce the official paths (no mystery URLs)
Reproduce this — Start from the AWS-maintained toolkit repo
aws/agent-toolkit-for-awsand follow the Quickstart for your assistant. Serverless-specific plugin sources live underawslabs/agent-plugins. Cross-check any CLI strings against the repo README—plugin marketplaces update frequently, and stale copy is a leading cause of “it worked in the blog” support threads.
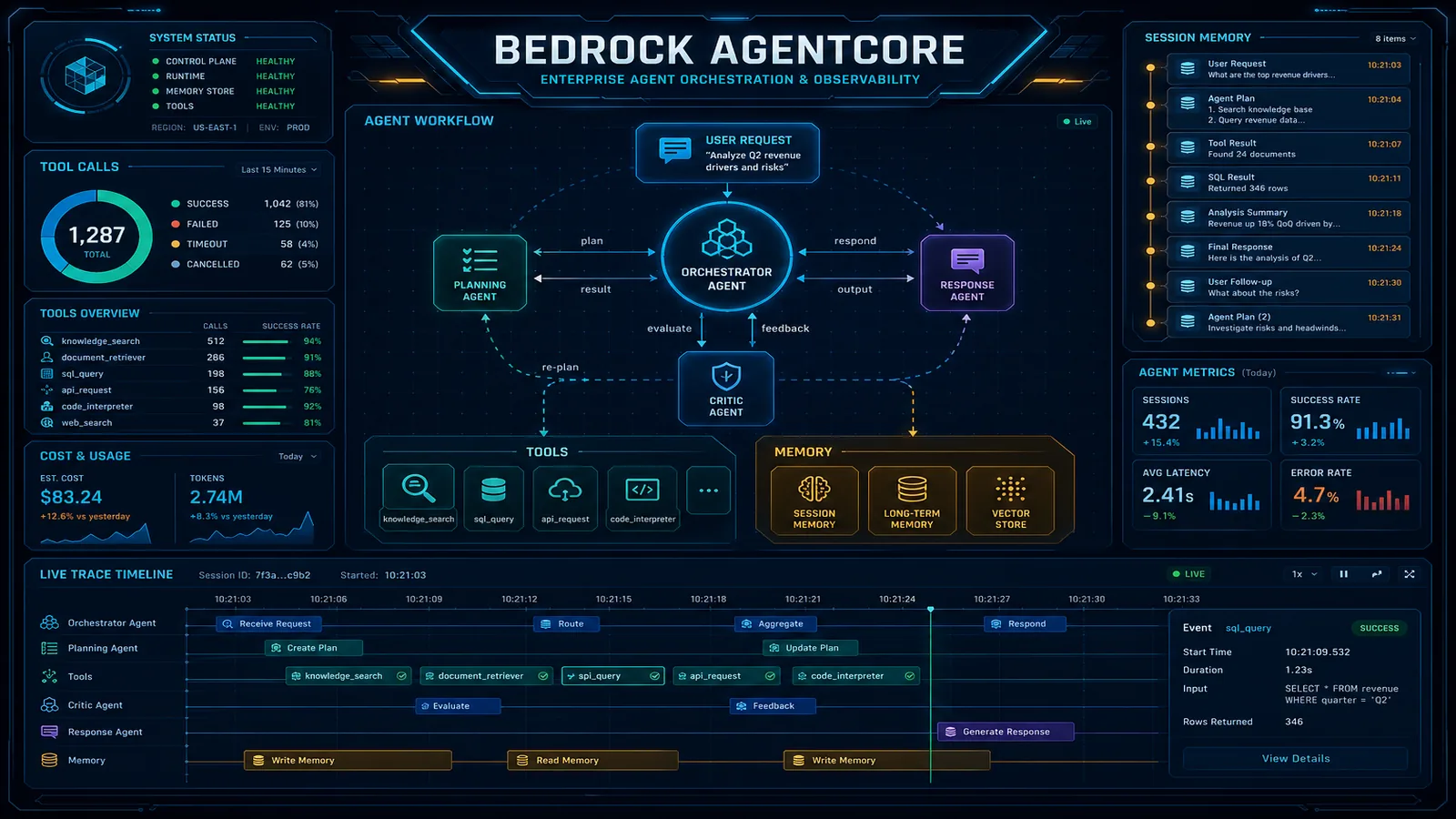
If you host agents on Amazon Bedrock AgentCore, review Deploy MCP servers in AgentCore Runtime alongside the GA announcement so you do not conflate runtime hosting with the managed AWS MCP Server product positioning.
What to do this week
- Read the GA sources first: AWS MCP Server GA (May 6, 2026) and Agent Plugin for AWS Serverless (Mar 25, 2026)—dates matter for your internal architecture decision log.
- Decide the trust boundary: will agents run against dev-only accounts this sprint, or do you need multi-account guardrails (SCPs + permission boundaries) before day one?
- Draft IAM as if the agent is a junior engineer with shell access: explicit denies for destructive actions in prod, separate roles per environment, no shared long-lived access keys on laptops.
- Instrument before you advertise: CloudWatch dashboards for agent-driven API volume; alerts on throttling, authorization failures, and sudden spikes in write-heavy services.
- Pair tooling: install or pilot the Serverless Agent Plugin where your pain is SAM/CDK/project scaffolding, not just “more MCP endpoints.”
If you only do one thing
Create a dedicated agent role per environment with CloudTrail-friendly naming and session context, then force every agent integration—managed MCP or otherwise—to assume that role through your standard federation pattern. Everything else gets easier once the principal is honest.
Field note—where teams usually feel the friction
Three questions that show up in almost every enterprise review — Security wants proof that agents are not equivalent to AdministratorAccess. Engineering wants velocity. Finance wants to know what happens if agents multiply write-heavy API traffic during an incident. The GA bundle (IAM + metrics + CloudTrail) supports the first and third threads when roles are intentionally narrow. It does not decide which mutations still require human approval—that is governance.
Related reading on FactualMinds
- AWS Agent Toolkit for AWS: every skill explained — walkthrough of
aws/agent-toolkit-for-aws: 13 skill categories, 43 atomicSKILL.mdpacks (snapshot at commit75023075), plugins (aws-core, aws-agents, aws-data-analytics), and how progressive disclosure keeps context small. - Kiro IDE and AWS agentic coding — how AWS-shaped agentic IDEs intersect with SSO and least privilege.
- AWS AI agents on Bedrock — when managed Bedrock Agents fit versus custom orchestration.
What this post does not cover
- Step-by-step wiring for every assistant’s MCP config JSON (those fragments drift weekly—use the official toolkit repo as source of truth).
- A full Bedrock AgentCore deployment guide—only a pointer where runtime MCP docs matter.
- Legal or procurement analysis of third-party assistants; your enterprise agreement and data processing terms still govern model vendors even when AWS hardens the AWS side.
Need help designing agent IAM, audit evidence, or a phased serverless rollout? FactualMinds is an AWS Select Tier Consulting Partner—tell us what you are building.
AWS Cloud Architect & AI Expert
AWS-certified cloud architect and AI expert with deep expertise in cloud migrations, cost optimization, and generative AI on AWS.