AWS IaC in 2026: Terraform vs OpenTofu vs Ansible — Practical Decision Guide
Quick summary: May 2026 guidance with a reproducible scaffold—9 artefact files, 0 Terraform-managed creates at plan baseline, and third-party comparisons refreshed Apr 24 and May 4, 2026.
Key Takeaways
- May 2026 guidance with a reproducible scaffold—9 artefact files, 0 Terraform-managed creates at plan baseline, and third-party comparisons refreshed Apr 24 and May 4, 2026
- On AWS specifically, layering all three blindly is where teams burn calendar on drift arguments
- Typical readers own change windows for VPC, RDS, EKS/ECS, or landing zones governed by tagging and SCP controls
- Decision 1 · Terraform versus OpenTofu (engine semantics on AWS) OpenTofu remains community-governed under MPL 2
- 0, emphasises OSS continuity, introduces native state encryption options absent from OSS Terraform lineage, and ships language conveniences—early variable evaluation highlighted from OpenTofu 1

Table of Contents
As of 11 May 2026, two widely cited comparison refreshes—Spacelift’s Ansible vs Terraform (updated 24 Apr 2026) and OpenTofu vs Terraform (4 May 2026)—still frame the IaC toolbox as three connected decisions, not one winner badge. Terraform and OpenTofu occupy the declarative infra lane; Ansible dominates mutable configuration and rollout choreography. On AWS specifically, layering all three blindly is where teams burn calendar on drift arguments.
This guide anchors each decision against VPC and Organizations realities (S3 remote state, DynamoDB state locks, SSM for hybrid transport) and bundles a reproducible scaffold: nine artefact files, zero Terraform-managed infrastructure at the baseline plan (read-only STS data sources only).
Who gets value from treating these as distinct choices
Pick this article if your platform team keeps Terraform plans green while Ansible inventories quietly rewrite packages, patches, agents, or app artifacts across Regions and accounts. Typical readers own change windows for VPC, RDS, EKS/ECS, or landing zones governed by tagging and SCP controls.
Decision 1 · Terraform versus OpenTofu (engine semantics on AWS)
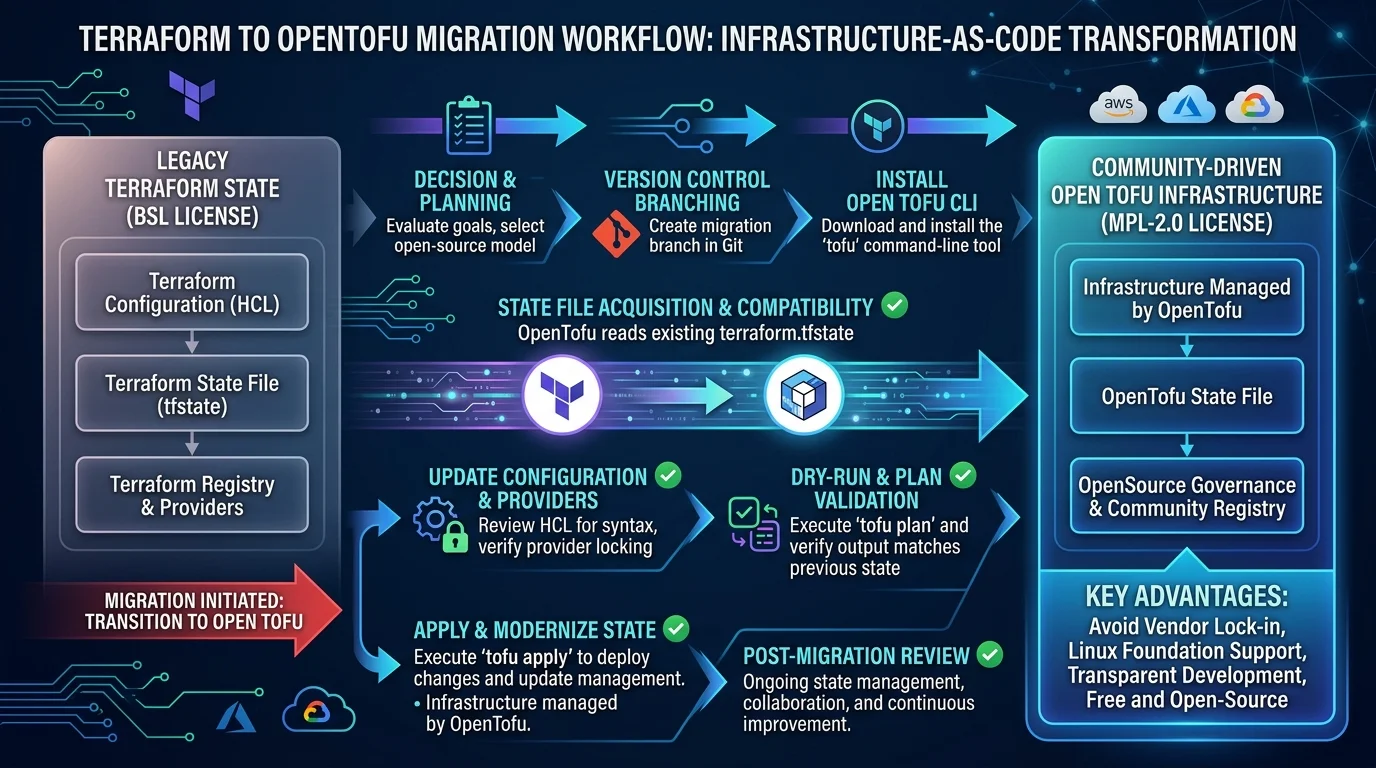
OpenTofu remains community-governed under MPL 2.0, emphasises OSS continuity, introduces native state encryption options absent from OSS Terraform lineage, and ships language conveniences—early variable evaluation highlighted from OpenTofu 1.8 onward (per contemporaneous tooling notes echoed in practitioner comparisons).
Terraform today ships under HashiCorp’s Business Source License (BSL): pragmatically fine for organisations automating AWS internally, but contentious for competing commercial hosted platforms resembling Terraform SaaS tiers. Licensing is not interchangeable with OSS guarantees.
Operational AWS guidance stays identical for both binaries at the grain we care about: same AWS provider, similar plan/apply graph, S3 + DynamoDB backends, IAM Identity Center workloads surfaced through standard credential chains.
Recommendation with trade-offs: choose OpenTofu when MPL-neutrality, community prioritisation dashboards, advanced state-protection features, or long-term OSS insurance outweigh chasing brand-new Terraform runtime flags first. Stick with Terraform when corporate purchasing or feature velocity through HashiCorp channels outweighs neutrality benefits. Migration mechanics already live separately in Migrate Terraform to OpenTofu—reuse that playbook instead of re-deriving it here.
Decision 2 · Terraform/OpenTofu versus Ansible on AWS workloads
Declarative infra tools model desired cloud resources, resolve dependencies implicitly, persist remote state, and shine when reproducing VPC topologies across staging versus production parity. Ansible orders tasks deliberately, excels at patching, systemd units, artefacts under /opt, language runtimes outside container images you already rebuilt, bootstrap tasks while images age, emergency triage SSH/SSM runbooks—even when infra objects stay unchanged.
Neither tool magically erases organisational boundaries: Ansible still crosses YAML playbook boundaries and role boundaries; Terraform forces module composition through graph edges and state addresses.
Typical AWS layering that survives audits
First publish immutable network + identity artefacts (aws_vpc, subnets, gateways, egress controls, RDS parameter groups baseline, foundational IAM roles) through Terraform/OpenTofu.
Second orchestrate fleet mutable surface—packages tuned per fleet, ephemeral tuning flags, JVM stack redeploy—not by hammering terraform destroy cycles but through AMI builds, aws_launch_template semver bumps, ansible-playbook over Systems Manager, or ephemeral container tasks.
Explicit hand-off uses Terraform outputs (private subnet IDs, RDS endpoints, aws_ssm_document URIs) consumed by Ansible variables or dynamically generated inventories.
Third hold golden image pipelines accountable for patching velocity; Ansible closes gaps CI cannot economically rebuild AMI for.
Edge cases AWS teams misunderstand until incident review
Ordering races after apply
EC2 may report running before userdata finishes or RDS exposes listeners inconsistently across Multi-AZ cutovers—Ansible patching too early wedges nodes half-configured until manual repair.
Provisioner-heavy Terraform as secret Ansible launcher
Treat remote_exec/local_exec nests as prototypes only: they conceal logs and break destroy semantics. Separate pipeline stages survive operational scrutiny.
Duplicate ownership hot spots
Teams grant Ansible playbooks carte blanche ec2_security_group modules while Terraform also manages the same aws_security_group. Divergent truth appears as _SG rule flapping, blocked SSH, or RDS Security Group regressions.
Drift detection philosophies differ
Terraform/OpenTofu surfaces drift through planned delta against state.
Ansible asserts desired package presence per host each run—it does not replace global infra inventories without complementary CMDB/export processes.
Instrument both in AWS Config remediation tickets only after naming owners.
Windows, hybrid identity, speciality partitions
Assume SSH-centric patterns fail on hardened Windows fleets—lean on Systems Manager.
Respect speciality regions/partitions credential profiles.
OpenTofu divergence watch
Bleeding-edge Terraform Experimental behaviours may diverge briefly—parity-test every minor bump with staging plans; optional .tofu files isolate OpenTofu-exclusive syntax.
Composite field note (anonymized) — A regulated B2B software provider spanning five payer AWS accounts (central networking plus product lines). Weekly drift appeared on VPC security groups: Terraform locked core networking patterns while Ansible crews occasionally re-opened legacy ingress during emergency patches until an ownership RACI moved every SG rule diff exclusively through the infra repo. Ansible retained package and service convergence only; networking PR noise dropped materially once reviewers stopped reconciling conflicting SG narratives.
Concrete engagement shapes vary widely; pairing immutable networking pipelines with narrowly scoped Ansible runbooks repeats across manufacturing, healthcare SaaS ISVs wrestling HIPAA segmentation, finance stacks behind VPC endpoints-only egress.
What broke — Midnight Ansible patching opened temporary SSH ingress tied to playbook authors’ home IPs. Morning Terraform reconcile removed the rule—but not before auditors flagged contradictory AWS Config timeline mismatches spanning twelve-hour change windows.
Reproduce this — Clone
examples/aws-iac-decision-demoon Bitbucket inside this repository.terraformortofu:terraform init -backend=falsethenterraform plan: baseline expectation Plan: 0 add, 0 change, 0 destroy assuming live STS credentials. Ansible: install collections (ansible-galaxy collection install -r ansible/requirements.yml), adjust inventory stub,ansible-playbook ... --check.
Nine tracked files underpin the scaffold (May 2026 snapshot); extend cautiously toward real modules.
Raw evidence surfaced by this artefact intentionally stays minimal—it proves provider wiring—not production blast radius sizing.
What to Do This Week
- Decide ownership matrix tagging (
terraform:root,ansible:mutable, forbidden dual-writer combos) for Security Groups, NACL-critical routes, IAM trust policies. - Create staging pipeline job emitting JSON plan artefacts—compare
terraformvstofuif licence evaluation active. - Inventory lingering provisioner usages; schedule removal or replacement with phased CI.
- Map AMI + launch template semver accountability vs Ansible-only mutation paths monthly.
- Link IAM Identity Center roles Terraform creates to CI runners with least privilege—including kms:Decrypt for SOPS envelopes if leveraging OpenTofu state helpers.
What This Post Doesn’t Cover
CDK, CloudFormation Org-level stacks, brownfield terraform import backlogs, granular Kyverno/OPA policy authoring, exhaustive GovCloud partitioning caveats beyond credential differences, exhaustive Pricing Model calculators, bespoke Landing Zone Accelerator substitutions, or platform-specific nuances of vendor Kubernetes distributions.
Consult specialist partners when entitlement boundaries intersect regulated HIPAA, SOC2, cross-border residency.
Further reading synthesising comparative angles
- Spacelift—Terraform vs Ansible: Differences and Comparison
- Spacelift—OpenTofu vs Terraform: Key Differences and Comparison
Interpret third-party summaries alongside current HashiCorp and OpenTofu release notes before governance meetings.
AWS Cloud Architect & AI Expert
AWS-certified cloud architect and AI expert with deep expertise in cloud migrations, cost optimization, and generative AI on AWS.