
10 AWS Cloud Security Best Practices: An Implementation Guide for 2026
Most AWS security breaches aren't caused by AWS failures — they're caused by misconfiguration. Here are 10 concrete best practices to harden your AWS environment in 2026.

Most AWS security breaches aren't caused by AWS failures — they're caused by misconfiguration. Here are 10 concrete best practices to harden your AWS environment in 2026.
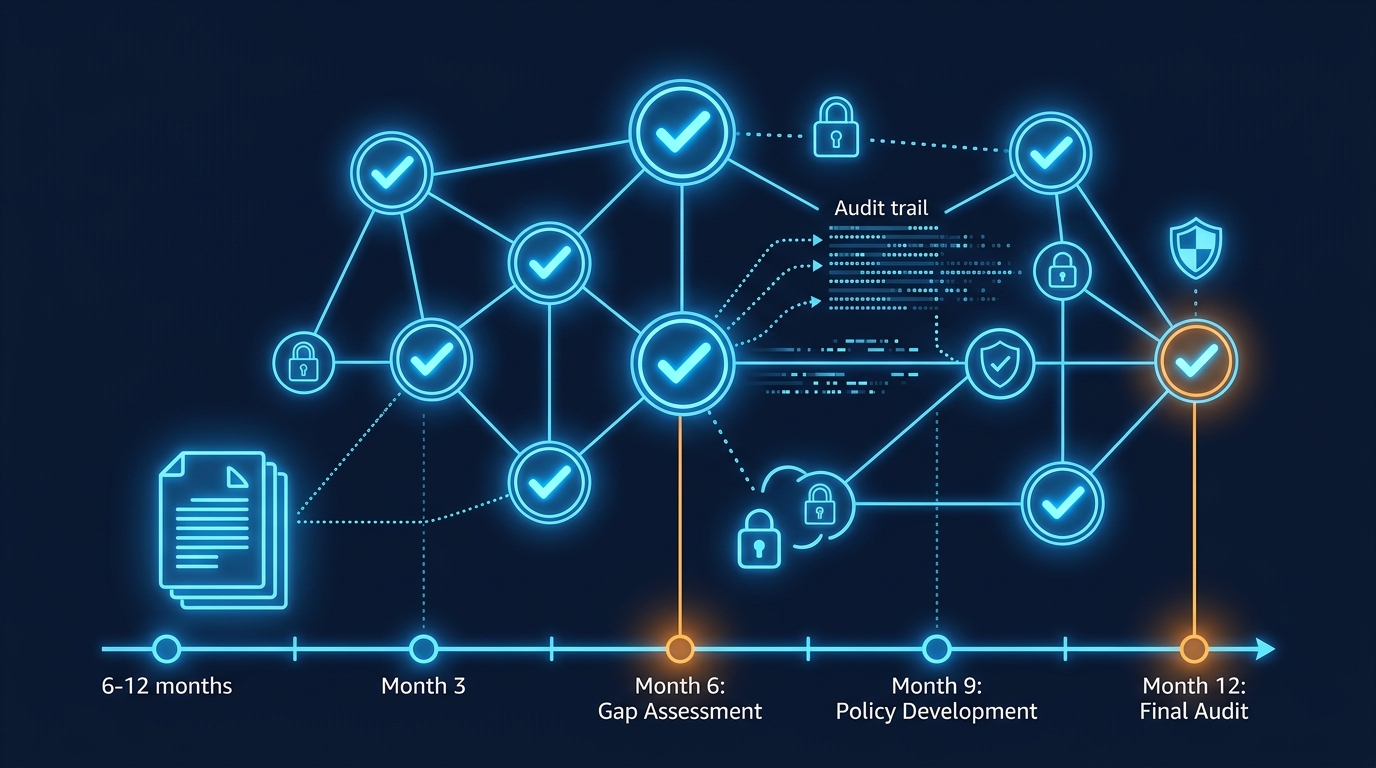
SOC 2 Type II certification proves your controls are effective over 6-12 months. This guide covers the compliance roadmap, AWS security controls, documentation requirements, and audit preparation for 2026 certification.

AWS WAF protects APIs from SQL injection, XSS, DDoS, and account takeover attacks. This guide covers advanced WAF rules, rate limiting, bot control, and production patterns for defending REST APIs and GraphQL endpoints.

HIPAA compliance on AWS requires encryption, audit logging, access controls, and Business Associate Agreements. This guide covers architecture patterns, AWS service configurations, and compliance validation for healthcare applications.

AWS Security Hub aggregates security findings from 200+ sources (GuardDuty, Config, IAM Access Analyzer, Inspector). This guide covers setup, compliance standards (PCI-DSS, CIS, NIST), automated remediation, and building a compliance dashboard without hiring a SOC team.

Attackers do not need to take down your service to hurt you — they can send traffic designed to maximize your AWS bill. DDoS amplification, Lambda invocation bombs, and SQS message flooding are billing attacks, not just availability attacks.

A practical architecture guide for PCI DSS compliance on AWS — CDE scoping, the 12 requirements mapped to AWS services, network design, encryption, logging, and audit readiness for payment-processing applications.
Manual security triage cannot keep up with cloud-scale threats. Here is how to wire GuardDuty Extended Threat Detection, Security Hub, EventBridge, and Lambda into a self-healing AWS security architecture.
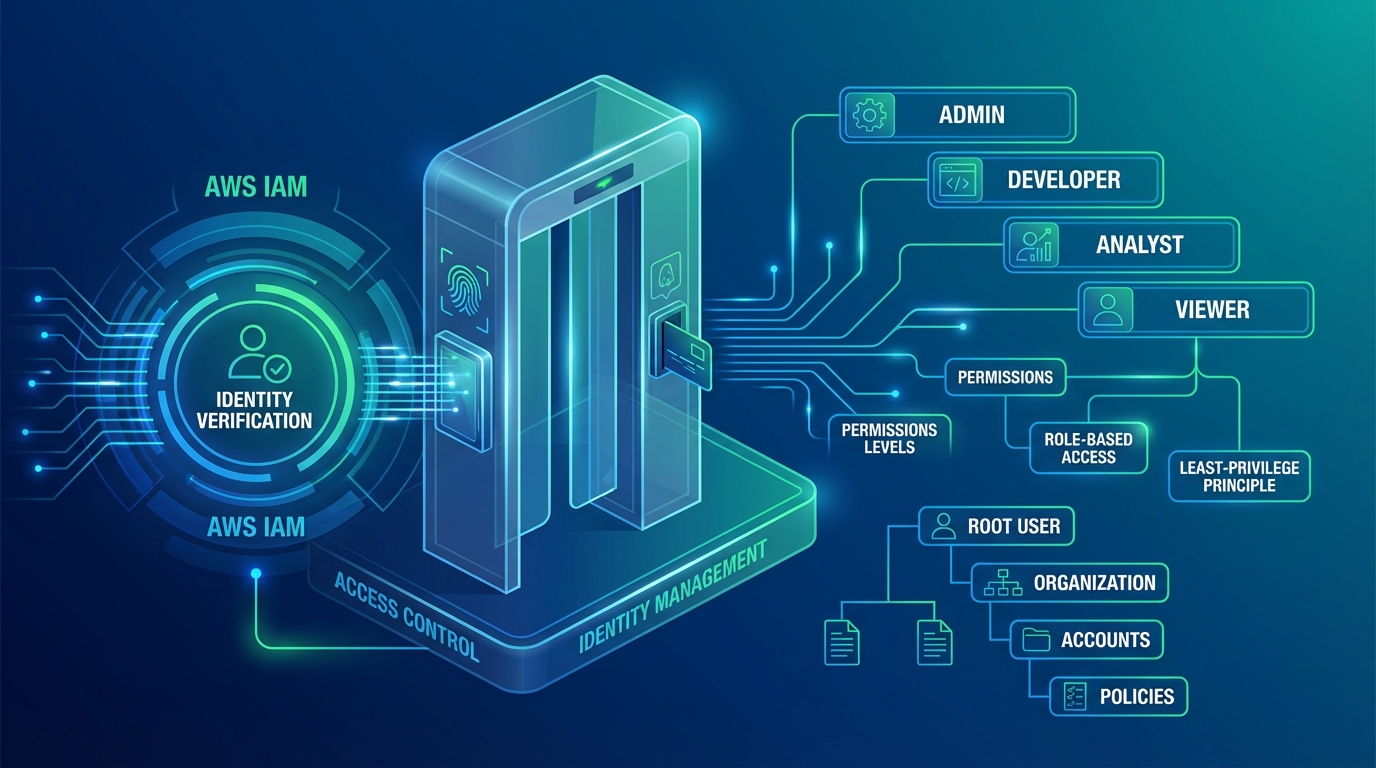
A practical guide to AWS IAM — least privilege policies, IAM roles vs users, permission boundaries, SCPs, identity federation, and the access control patterns that secure production workloads without slowing teams down.

A practical comparison of AWS Secrets Manager and SSM Parameter Store — pricing, rotation, encryption, cross-account access, and clear guidelines for when to use each service for secrets and configuration management.

A practical guide to AWS WAF for production web applications — managed rule groups, custom rules, rate limiting, bot control, and the layered defense strategy that protects without blocking legitimate traffic.

A comprehensive guide to S3 security — bucket policies, encryption, access logging, Block Public Access, and the practices that prevent the data breaches that make headlines.
We use cookies and similar technologies to analyze site traffic, personalize content, and provide social media features. By clicking "Accept," you consent to our use of cookies. You can adjust your preferences at any time.