From Reactive to Proactive: Automating AWS Security Remediation with AI-Driven Threat Detection
Quick summary: Manual security triage cannot keep up with cloud-scale threats. Here is how to wire GuardDuty Extended Threat Detection, Security Hub, EventBridge, and Lambda into a self-healing AWS security architecture.
Key Takeaways
- Here is how to wire GuardDuty Extended Threat Detection, Security Hub, EventBridge, and Lambda into a self-healing AWS security architecture
- Here is how to wire GuardDuty Extended Threat Detection, Security Hub, EventBridge, and Lambda into a self-healing AWS security architecture
Table of Contents
There was a time when a security incident meant someone’s pager went off at 2 a.m. A human pulled up a dashboard, read through a wall of alerts, triaged manually, and — if the threat was serious enough — kicked off a remediation runbook that lived in a shared document somewhere. That model worked when infrastructure was ten servers sitting in a colocation rack. It breaks down completely when your attack surface spans dozens of AWS accounts, hundreds of microservices, and petabytes of data distributed across S3 buckets in multiple regions.
The honest problem with reactive security is not that your team is slow. It is that the threat moves faster than any human response cycle can match. According to industry benchmarks, the global average time to identify and contain a cloud breach remains stubbornly high — identification alone averages around 194 days, with weeks more to fully contain the incident. Every one of those days is dwell time: time an attacker spends moving laterally, escalating privileges, and exfiltrating data. Top-performing security teams now target critical-severity mean time to remediate (MTTR) under one hour. The gap between average and best-in-class is measured in regulatory fines, reputational damage, and millions of dollars of direct exposure.
Closing that gap is not a headcount problem. It is an architecture problem.
Why Reactive Security Cannot Scale in the Cloud
Cloud infrastructure is dynamic by design. Auto-scaling groups launch and terminate instances based on load. Lambda functions execute for milliseconds and disappear. ECS tasks spin up and down within minutes. When every component is ephemeral and every configuration is code, the blast radius of a single compromised credential or misconfigured security group expands at machine speed — not human speed.
Manual investigation was never designed for this environment. By the time a SOC analyst has correlated a suspicious IAM API call with an unusual data transfer pattern, traced it back to a specific EC2 instance, and confirmed lateral movement, the damage is already done. What security teams need is not faster analysts. They need threat detection that correlates signals automatically across every layer of the stack, and response workflows that execute remediation before a human has even opened the alert.
The AI Layer: What GuardDuty Extended Threat Detection Actually Does
Amazon GuardDuty has been the foundation of AWS threat detection for years, continuously analyzing tens of billions of events across CloudTrail management logs, VPC Flow Logs, DNS queries, S3 data events, and runtime activity for EKS, EC2, ECS, and Fargate workloads. What changed meaningfully at re:Invent 2024 — and expanded in December 2025 to cover EC2 and ECS — is GuardDuty Extended Threat Detection.
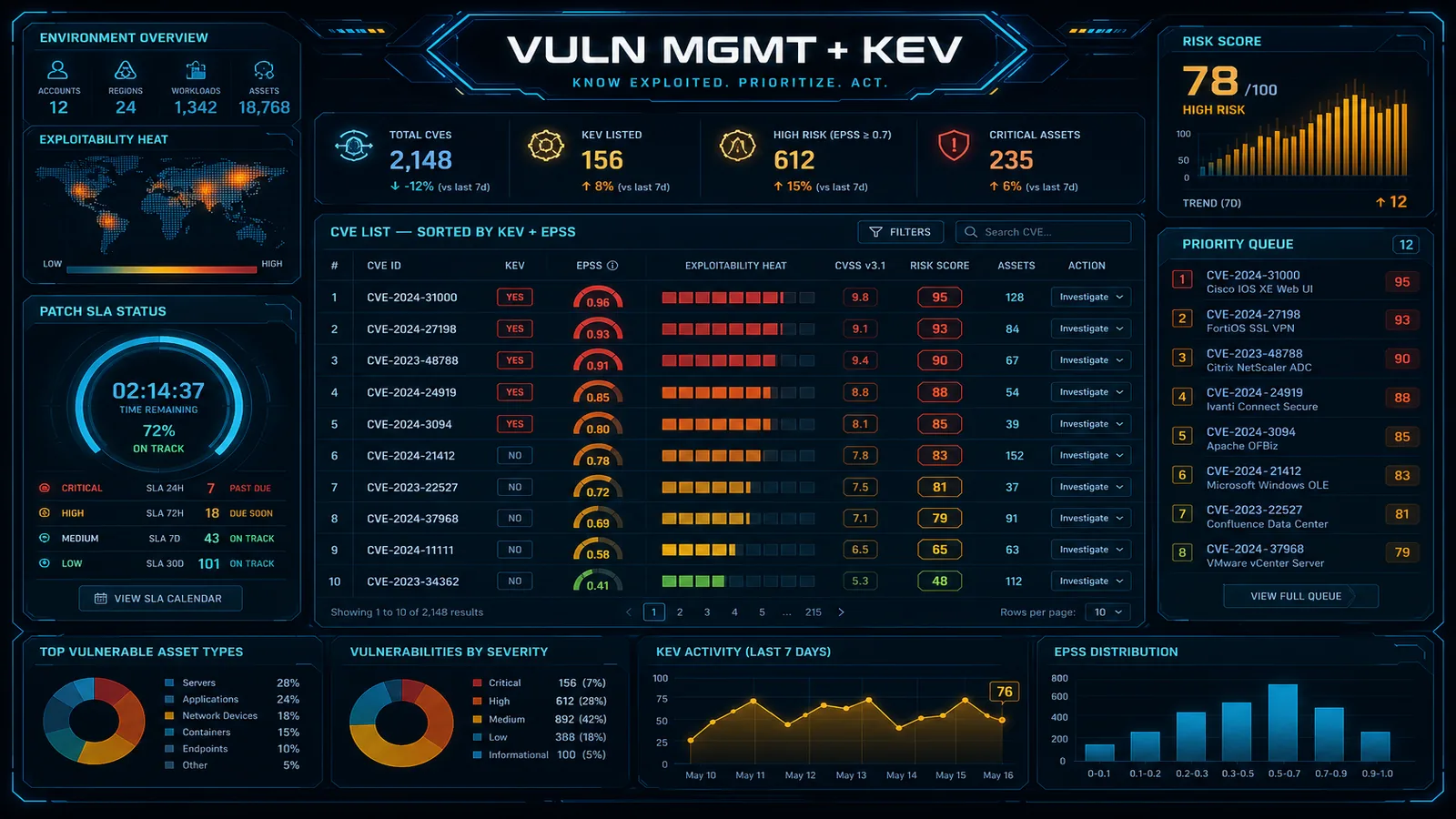
This is where monitoring becomes intelligence. Extended Threat Detection uses AI and ML models trained at AWS scale to automatically correlate security signals across multiple data sources and identify multi-stage attack sequences — not just isolated anomalies. A standalone finding like UnauthorizedAccess:IAMUser/ConsoleLoginSuccess tells you a login occurred from an unusual location. An attack sequence finding tells you that login was followed by IAM privilege escalation, which was followed by large-scale S3 GetObject requests consistent with data exfiltration — and it presents that entire chain as a single critical-severity finding, mapped to MITRE ATT&CK tactics and techniques, with a human-readable incident summary and specific remediation recommendations built in.
As of December 2025, Extended Threat Detection covers EC2 and ECS workloads with findings like AttackSequence:EC2/CompromisedInstanceGroup and AttackSequence:ECS/CompromisedCluster. You are no longer chasing individual alerts and mentally reconstructing the attack narrative. GuardDuty does that reconstruction for you, automatically.
The Automation Stack: Building Self-Healing Infrastructure
Detection without response is just better alerting. The architectural pattern that turns GuardDuty findings into actual automated remediation looks like this:
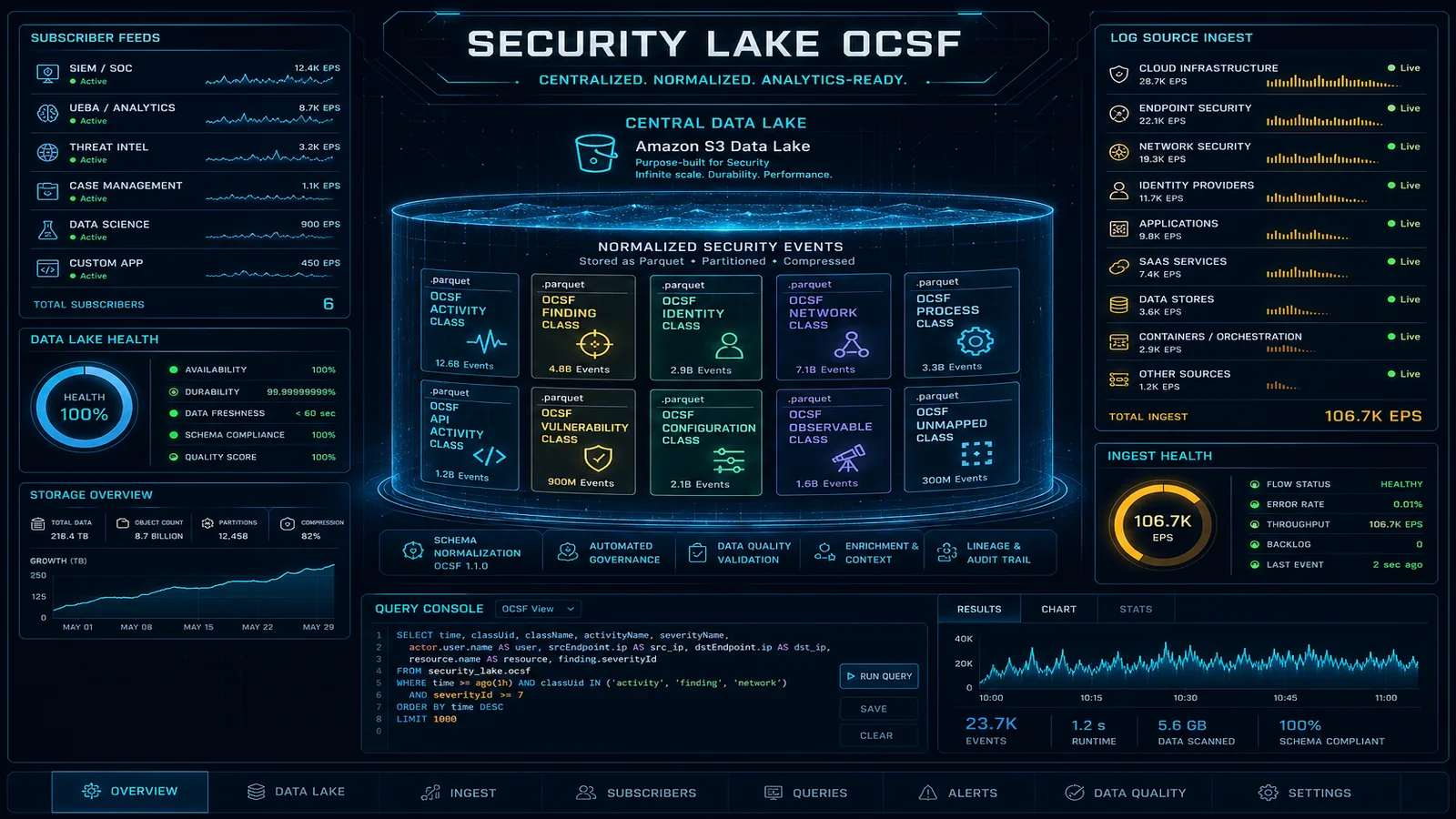
GuardDuty → Security Hub → EventBridge → Lambda → SSM AutomationAWS Security Hub aggregates findings from GuardDuty, Inspector, Macie, and Firewall Manager into a unified view normalized to the AWS Security Finding Format (ASFF). EventBridge rules listen for those findings in near-real time and route them to the appropriate Lambda-based remediation playbook. For complex, multi-step workflows — isolating a compromised instance, revoking IAM credentials, snapshotting memory and disk for forensic analysis — Lambda invokes AWS Systems Manager Automation Documents (SSM Runbooks) to orchestrate each step with full retry logic and error handling. Every action is logged back to CloudWatch, finding notes in Security Hub are updated throughout, and the finding is marked RESOLVED only after the remediation is verified. The result is a complete audit trail with zero manual documentation effort.
What This Looks Like End-to-End
GuardDuty raises an AttackSequence:EC2/CompromisedInstanceGroup finding at 2:14 a.m. EventBridge matches the pattern and triggers a Lambda function within seconds. That function calls an SSM Runbook that: moves the affected instances into a quarantine security group (blocking all inbound and outbound traffic except a forensics bastion), revokes active sessions for the associated IAM role, triggers memory and disk snapshots, and pushes a structured incident summary to the security team via SNS. By 2:15 a.m., the threat is contained, evidence is preserved, and the on-call engineer wakes up to a resolved ticket with a complete timeline — rather than a raw alert and a blank terminal.
That is self-healing infrastructure in practice.
Automation Without Guardrails Creates Its Own Risks
Blind automation can cause cascading failures that rival the original incident. Isolating the wrong EC2 instance in a production cluster during peak hours is its own outage. The right pattern is graduated automation, calibrated to severity:
| Severity | Automated Action | Human Involvement |
|---|---|---|
| Low / Medium | Auto-remediate, log, notify | Review during business hours |
| High | Auto-contain (isolate, revoke sessions), notify | Approval required to restore |
| Critical / Attack Sequence | Auto-contain + forensic snapshot + immediate page | Post-incident review required |
A few implementation details that matter in production:
- Filter EventBridge rules by control ID, not control title. AWS periodically updates Security Hub control titles and descriptions. Control IDs are stable identifiers. Filtering by title will silently break your automation the next time a control description changes.
- Scope Lambda execution roles with least-privilege IAM. A remediation function that quarantines EC2 instances has no business with S3 write permissions. Scope every execution role precisely to what that specific playbook requires.
- Validate remediation before closing findings. Confirm the SSM Runbook completed successfully before marking a Security Hub finding as resolved. A failed remediation that closes a finding is worse than no automation — it creates a false sense of security.
- Start with the AWS Automated Security Response solution. AWS maintains a deployable solution with pre-built playbooks covering dozens of common Security Hub findings. It is a significantly faster starting point than building the entire stack from scratch.
What This Means for Your Organization
For CTOs and IT Managers: Automated remediation compresses MTTR from hours to minutes, eliminates analyst toil on repetitive triage tasks, and generates the audit trails that SOC 2, PCI DSS, and HIPAA require — without manual documentation effort. Security posture becomes a measurable, improvable system metric rather than a function of how quickly your team can respond on a given day.
For Cloud Architects: This is AI operating at the infrastructure layer — correlating signals across heterogeneous data sources, reconstructing attack narratives that would take a human analyst hours to piece together, and feeding structured, MITRE-mapped findings into deterministic automation pipelines. It is a meaningfully different capability from embedding a foundation model in a chat interface.
For DevOps Leads: The same event-driven pattern that underpins operational automation — EventBridge triggering Lambda, Lambda invoking SSM — applies directly to security remediation. Your infrastructure can now respond to a compromised instance the same way it responds to a failed health check: automatically, consistently, and with a full audit trail. Security becomes a property of the system, not a dependency on the availability of a specific engineer.
The Stack Is Ready — The Question Is Whether You Are
The full capability stack — GuardDuty Extended Threat Detection, Security Hub, EventBridge, Lambda, Systems Manager Automation — is available today on AWS. It requires no custom machine learning infrastructure, no third-party security platforms, and no agents on your instances for the core detection layer. What it does require is intentional architecture: connecting the services correctly, building graduated playbooks, and putting the right guardrails in place before enabling automated actions in production.
The organizations that get this right will spend less on security operations, respond to threats faster, and have demonstrably better audit posture. The ones that remain reactive will continue paying the cost — in analyst burnout, compliance findings, and breach exposure — of treating cloud security like it is still 2015.
FactualMinds is an AWS Select Tier Consulting Partner. We design and implement automated security architectures on AWS — from GuardDuty Extended Threat Detection to full self-healing remediation pipelines. For organizations with compliance requirements, see our Cloud Compliance Services. Talk to our team about a security architecture review.
References
- Amazon GuardDuty – Intelligent Threat Detection
- Introducing GuardDuty Extended Threat Detection – AWS News Blog
- GuardDuty Extended Threat Detection for EC2 and ECS – AWS News Blog
- Using EventBridge for Automated Response – AWS Security Hub Docs
- Automated Security Response on AWS – AWS Solutions Library
- MTTD and MTTR in Cybersecurity – Wiz Academy
- MITRE ATT&CK Framework
AWS Cloud Architect & AI Expert
AWS-certified cloud architect and AI expert with deep expertise in cloud migrations, cost optimization, and generative AI on AWS.