SaaS Multi-Tenancy on AWS: Silo vs Pool vs Bridge Model
Quick summary: A practical guide to SaaS multi-tenancy architecture on AWS — comparing silo, pool, and bridge isolation models with trade-offs for cost, security, compliance, and operational complexity.
Key Takeaways
- A practical guide to SaaS multi-tenancy architecture on AWS — comparing silo, pool, and bridge isolation models with trade-offs for cost, security, compliance, and operational complexity
- A practical guide to SaaS multi-tenancy architecture on AWS — comparing silo, pool, and bridge isolation models with trade-offs for cost, security, compliance, and operational complexity
Table of Contents
Every SaaS company faces the same foundational architecture decision: how do you isolate tenants from each other? The answer affects your infrastructure cost, security posture, compliance capabilities, operational complexity, and ability to scale. Get it wrong early, and you will spend years refactoring — or worse, explaining a data breach to your customers.
This guide covers the three primary multi-tenancy models on AWS, the trade-offs between them, and a practical decision framework for choosing the right approach.
What Multi-Tenancy Means
Multi-tenancy is the practice of serving multiple customers (tenants) from shared infrastructure. The question is not whether to share — purely single-tenant deployments are prohibitively expensive for most SaaS businesses — but how much to share and where to draw isolation boundaries.
Tenancy decisions apply at every layer of your stack:
- Compute — Do tenants share the same Lambda functions, containers, or EC2 instances?
- Database — Do tenants share the same database, the same tables, or have completely separate databases?
- Networking — Do tenants share the same VPC, subnets, and security groups?
- Storage — Do tenants share the same S3 buckets and prefixes?
- Identity — Do tenants share the same Cognito user pool or have separate pools?
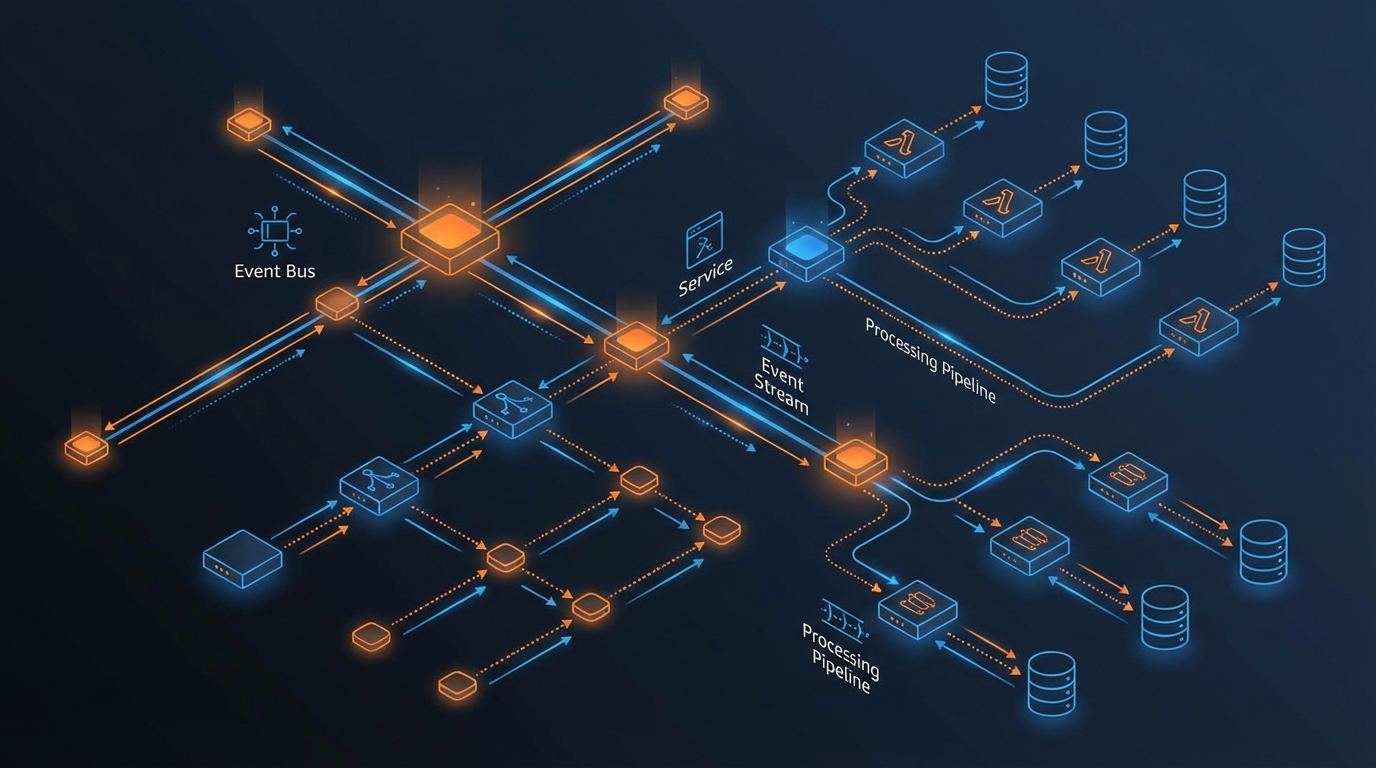
The Three Models
Model 1: Silo (Full Isolation)
In the silo model, each tenant gets a completely separate set of infrastructure resources — their own database, their own compute, their own storage.
AWS architecture:
Tenant A: VPC-A → ALB-A → ECS Service-A → RDS Instance-A → S3 Bucket-A
Tenant B: VPC-B → ALB-B → ECS Service-B → RDS Instance-B → S3 Bucket-B
Tenant C: VPC-C → ALB-C → ECS Service-C → RDS Instance-C → S3 Bucket-CAdvantages:
- Strongest isolation — No shared resources means no risk of cross-tenant data leakage at the infrastructure level
- Per-tenant customization — Each tenant can run a different version, configuration, or even different features
- Per-tenant scaling — Scale resources independently based on each tenant’s actual usage
- Simplified compliance — Data residency, encryption keys, and access controls are inherently per-tenant
- Blast radius containment — A bug or outage affecting one tenant’s infrastructure does not affect others
Disadvantages:
- Highest cost — Every tenant incurs baseline infrastructure costs (minimum RDS instance, minimum ECS tasks, ALB, NAT Gateway)
- Operational complexity at scale — Managing 100 separate database instances, 100 ECS services, and 100 monitoring configurations is exponentially harder than managing one
- Slow tenant onboarding — Provisioning a full infrastructure stack per tenant takes minutes to hours
- Deployment overhead — Rolling out a new version requires deploying to every tenant’s stack individually
Cost example: A silo deployment with a minimum viable stack per tenant (t3.small RDS, 2 Fargate tasks, ALB, NAT Gateway) costs roughly $250-$400/month per tenant in AWS infrastructure alone. At 100 tenants, that is $25,000-$40,000/month before any application cost.
Best for: Enterprise SaaS with fewer than 50 high-value tenants, healthcare/finance with strict compliance requirements, tenants who demand data isolation guarantees.
Model 2: Pool (Shared Everything)
In the pool model, all tenants share the same infrastructure. Isolation is enforced at the application layer through tenant-aware code.
AWS architecture:
All Tenants → ALB → ECS Service (shared) → RDS (shared, tenant_id column) → S3 (shared, tenant prefix)Every database query includes a tenant filter:
SELECT * FROM orders WHERE tenant_id = 'tenant-a' AND order_date > '2026-01-01'Advantages:
- Lowest cost per tenant — Infrastructure cost is amortized across all tenants. Adding the 101st tenant costs virtually nothing
- Simplest operations — One database to monitor, one service to deploy, one set of alarms to manage
- Fastest onboarding — Adding a tenant is a database row, not an infrastructure deployment
- Uniform deployment — One deployment updates all tenants simultaneously
Disadvantages:
- Noisy neighbor risk — One tenant’s heavy query can degrade performance for all tenants
- Cross-tenant data risk — A missing
WHERE tenant_id = ?clause in any query leaks data across tenants. This is the most common SaaS security vulnerability - Compliance limitations — Some regulations require dedicated infrastructure per customer (or at minimum, dedicated encryption keys and access controls)
- Scaling ceiling — Eventually, the shared database becomes a bottleneck that requires sharding or migration to a silo model
Cost example: A pool deployment with a shared stack (db.r6g.large RDS, 4 Fargate tasks, ALB) costs roughly $800-$1,200/month total. At 100 tenants, that is $8-$12/month per tenant.
Best for: SMB-focused SaaS with hundreds or thousands of tenants, early-stage startups optimizing for speed and cost, products where tenant data sensitivity is low.
Model 3: Bridge (Hybrid)
The bridge model combines silo and pool approaches — sharing some resources while isolating others based on the sensitivity and performance characteristics of each layer.
Common bridge patterns on AWS:
Pattern A — Shared compute, isolated data:
All Tenants → ALB → ECS Service (shared) → RDS Instance per tenant → S3 Bucket per tenantPattern B — Shared everything, isolated by tier:
Free/SMB Tenants → Shared pool
Enterprise Tenants → Individual siloPattern C — Shared infrastructure, isolated schemas:
All Tenants → ALB → ECS Service (shared) → RDS (shared instance, schema per tenant)Advantages:
- Balanced cost and isolation — Share infrastructure where it is safe (compute, networking) while isolating where it matters (data)
- Tiered offerings — Offer pool for standard plans and silo for enterprise plans at different price points
- Pragmatic compliance — Meet data isolation requirements without the full cost of silo
- Flexible evolution — Start with pool, migrate high-value tenants to silo as they demand it
Disadvantages:
- Architectural complexity — Your application must handle multiple deployment models, which increases code complexity
- Operational overhead — You are managing a mix of shared and dedicated resources, which complicates monitoring and deployment
- Testing burden — You need to test every feature in both pool and silo configurations
Best for: SaaS products serving both SMB and enterprise customers, products that need to offer different isolation tiers, mature products evolving from pool to selective silo.
AWS Services for Multi-Tenancy
Database Layer
| Strategy | AWS Service | Isolation Level | Cost |
|---|---|---|---|
| Separate instances | RDS, Aurora | Full (silo) | $$$ |
| Separate schemas | RDS, Aurora | Schema-level | $$ |
| Shared tables with tenant_id | RDS, Aurora, DynamoDB | Row-level (pool) | $ |
| Separate tables | DynamoDB | Table-level | $$ |
| Separate accounts | Any | Account-level | $$$$ |
DynamoDB is naturally suited for multi-tenancy because its partition key can include the tenant ID:
PK: TENANT#tenant-a#ORDER#12345
SK: 2026-03-10T14:30:00ZThis provides logical isolation with the cost efficiency of a shared table. DynamoDB’s access patterns are always key-based, which eliminates the “missing WHERE clause” risk that plagues SQL-based pool models.
Compute Layer
Lambda — Naturally pooled. All tenants invoke the same function. Tenant context is passed in the event payload. Concurrency limits can be set per tenant using reserved concurrency.
ECS/Fargate — Can be deployed as pool (shared service, tenant in request header), silo (service per tenant), or bridge (shared service with tenant-specific task definitions for heavy hitters).
EKS — Kubernetes namespaces provide logical isolation. Network policies restrict cross-namespace traffic. Pod-level resource quotas prevent noisy neighbor issues.
Identity and Access
Cognito — Supports both pool (shared user pool with custom attributes for tenant) and silo (user pool per tenant). Silo user pools provide stronger isolation but increase management overhead.
IAM — Use IAM policies with condition keys to restrict access to tenant-specific resources:
{
"Condition": {
"StringEquals": {
"s3:prefix": "tenants/${aws:PrincipalTag/tenant-id}/"
}
}
}Networking
VPC — Silo tenants can have separate VPCs. Pool tenants share a VPC with security groups providing network-level controls.
API Gateway — Usage plans and API keys provide per-tenant rate limiting and throttling. Custom domain names can provide tenant-specific endpoints (tenant-a.api.example.com).
Tenant Isolation Patterns
Regardless of which model you choose, you need defense-in-depth isolation:
Application-Level Isolation
- Tenant context injection — Extract tenant ID from JWT token or API key at the API gateway and inject it into every downstream request
- Middleware enforcement — A middleware layer that adds tenant filters to every database query automatically, preventing developers from accidentally omitting the filter
- Testing — Automated tests that verify cross-tenant data access is impossible
Infrastructure-Level Isolation
- IAM policies — Scope IAM roles to tenant-specific resources using condition keys
- Encryption — Per-tenant KMS keys for data encryption at rest (required for some compliance frameworks)
- Network isolation — Security groups, NACLs, or separate VPCs depending on isolation requirements
Monitoring and Observability
- Per-tenant metrics — CloudWatch custom metrics with tenant dimension for monitoring per-tenant latency, error rates, and resource consumption
- Per-tenant cost attribution — AWS cost allocation tags to track infrastructure cost per tenant
- Noisy neighbor detection — Alerts when any single tenant consumes disproportionate resources
Decision Framework
Use this framework to guide your tenancy model selection:
Start with Pool If:
- You are pre-product-market fit and optimizing for development speed
- Your tenants are SMBs with low data sensitivity
- You have fewer than 10,000 rows per tenant (data volume is small)
- You do not have compliance requirements mandating data isolation
- Your engineering team is small (under 10 engineers)
Start with Silo If:
- Your tenants are enterprises paying $10,000+/month
- You have compliance requirements (HIPAA, SOC 2 with dedicated infrastructure, FedRAMP)
- Tenants have wildly different performance requirements
- You have fewer than 50 tenants
- Cross-tenant data leakage would be catastrophic (financial, healthcare)
Start with Bridge If:
- You serve both SMB and enterprise customers
- You want to offer tiered isolation as a paid feature
- You have 50-500 tenants with a mix of usage patterns
- You need compliance readiness for some (not all) tenants
Re-Evaluate When:
- Pool at 10,000+ tenants — Shared database may need sharding or migration to a purpose-built solution
- Silo at 100+ tenants — Operational overhead of managing hundreds of stacks becomes unsustainable without significant automation
- Bridge always — Continuously assess whether the complexity of supporting multiple models is justified by the business value
Common Multi-Tenancy Mistakes
Mistake 1: Choosing Silo Too Early
Startups sometimes choose silo because it seems “more secure.” The result: $5,000/month in infrastructure for 5 tenants paying $500/month each. The business cannot afford to scale because every new customer adds significant infrastructure cost. Start with pool, add silo for enterprise customers when the revenue justifies it.
Mistake 2: No Tenant Context Enforcement
In a pool model, relying on developers to remember WHERE tenant_id = ? in every query is a data breach waiting to happen. Use an ORM middleware, database row-level security (RDS PostgreSQL), or DynamoDB partition key design to enforce tenant isolation at the infrastructure level, not the application level.
Mistake 3: Ignoring Noisy Neighbors
A single tenant running a heavy export or analytics query in a pool model can degrade performance for every other tenant. Implement per-tenant concurrency limits, query timeouts, and rate limiting from day one — not after the first customer complaint.
Mistake 4: No Per-Tenant Cost Tracking
Without cost attribution, you cannot tell whether your largest tenant is profitable or losing money. Tag all AWS resources with tenant identifiers and track per-tenant infrastructure cost monthly. This data is critical for pricing decisions and capacity planning.
Getting Started
Multi-tenancy architecture is a foundational decision that affects every layer of your SaaS platform. Getting it right requires understanding your tenant profiles, compliance requirements, and growth trajectory.
For architecture design and implementation of multi-tenant applications on AWS, including compute, database, identity, and isolation strategies, see our AWS Architecture Review services.
For ongoing operational management of your SaaS platform, see our AWS Managed Services.
AWS Cloud Architect & AI Expert
AWS-certified cloud architect and AI expert with deep expertise in cloud migrations, cost optimization, and generative AI on AWS.