Running HIPAA-Compliant AI on AWS Bedrock
Quick summary: Deploy HIPAA-compliant AI on AWS Bedrock: encryption, data handling, and compliance architecture for healthcare.
Key Takeaways
- Deploy HIPAA-compliant AI on AWS Bedrock: encryption, data handling, and compliance architecture for healthcare
- Deploy HIPAA-compliant AI on AWS Bedrock: encryption, data handling, and compliance architecture for healthcare

Table of Contents
HIPAA + AI on Bedrock: A Powerful Combination
AWS Bedrock is HIPAA-eligible. With proper configuration, you can deploy generative AI in healthcare without violating HIPAA regulations. This guide covers the technical and compliance requirements.
What Makes Bedrock HIPAA-Eligible
Encryption
- Data in transit: TLS 1.2+ (enforced)
- Data at rest: AES-256 with KMS (required)
- Bedrock doesn’t store data; processes and returns
Data Isolation
- Data stays in your AWS account
- Anthropic (Claude creator) cannot access patient data
- AWS can view encrypted data (standard cloud)
Audit Trail
- CloudTrail logs all API calls
- Who called Bedrock, when, what parameters
- Meets HIPAA audit requirements
Business Associate Agreement (BAA)
- AWS must sign BAA with healthcare organization
- Establishes contractual compliance obligations
- Required before processing patient data
HIPAA Compliance Checklist for Bedrock
Before Using Patient Data:
- ☐ Sign AWS BAA for Bedrock
- ☐ Sign AWS BAA for CloudTrail, CloudWatch, KMS
- ☐ Enable KMS encryption on all data
- ☐ Configure VPC (no internet exposure)
- ☐ Enable CloudTrail logging
- ☐ Document data flows and retention policies
Application Level:
- ☐ De-identify PII where possible
- ☐ Don’t log prompts/responses with patient data
- ☐ Encrypt prompts before sending to Bedrock
- ☐ Restrict access via IAM roles
- ☐ Implement audit logging
- ☐ Regular access reviews
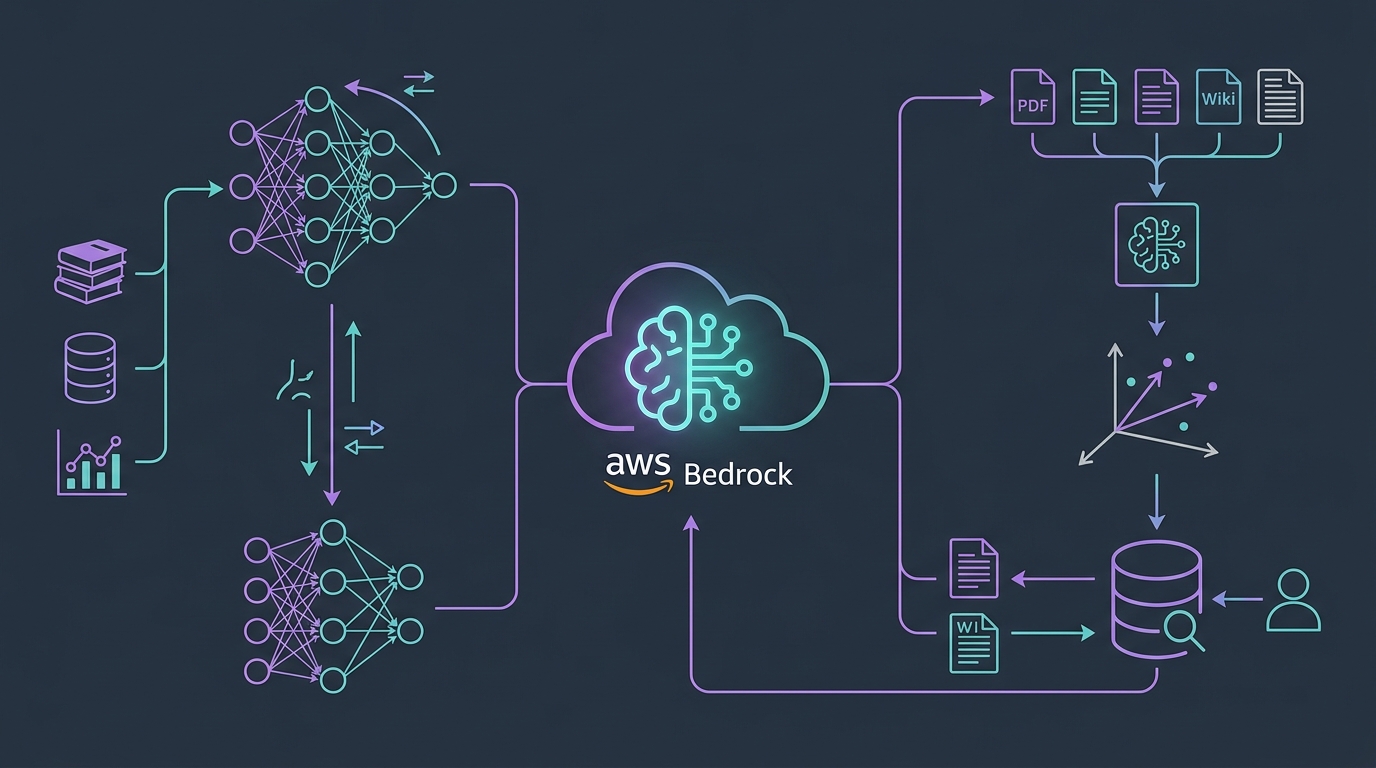
Architecture: HIPAA-Compliant AI Workflow
Patient Data (EHR)
↓ (encrypted)
VPC Private Subnet
↓
Lambda Function (HIPAA-logging enabled)
↓
Bedrock (within VPC via VPC Endpoint)
↓
KMS Encryption/Decryption
↓
CloudTrail (audit logs)
↓
Response (encrypted, returned)
↓
EHR (encrypted storage)Key Points:
- All data movement encrypted (KMS)
- VPC Endpoint for Bedrock (no internet exposure)
- CloudTrail logs every access
- IAM controls who can access
Allowed vs Prohibited Use Cases
Allowed (Informational/Administrative)
- Summarize clinical notes for provider review
- Generate patient education materials
- Appointment scheduling assistance
- Symptom checker (marked as informational)
- Medical transcription improvement
- Drug interaction checking (informational)
Prohibited (Clinical Decision)
- Treatment recommendations
- Diagnostic decisions
- Medication dosing
- Replacing physician judgment
Gray Area (Requires Careful Design)
- Clinical decision support (must include provider oversight)
- Risk scoring (informational only)
- Research analysis (cannot identify individuals)
Data Protection Implementation
1. Encrypt Sensitive Data
import boto3
from botocore.exceptions import ClientError
kms = boto3.client('kms')
# Encrypt patient data before processing
patient_data = "Patient: John Doe, DOB: 01/15/1980, Chief Complaint: Chest pain"
response = kms.encrypt(
KeyId='arn:aws:kms:us-east-1:ACCOUNT:key/KEY_ID',
Plaintext=patient_data
)
encrypted = response['CiphertextBlob']2. Call Bedrock with Encrypted Data
bedrock = boto3.client('bedrock-runtime')
# Send encrypted prompt to Bedrock
response = bedrock.invoke_model(
modelId='anthropic.claude-3-5-sonnet-20241022-v2:0',
body=json.dumps({
'prompt': f'Summarize this clinical note: {encrypted}',
'max_tokens': 500
})
)3. Decrypt Response
decrypted = kms.decrypt(CiphertextBlob=response_encrypted)
plaintext = decrypted['Plaintext'].decode('utf-8')Compliance Audit Requirements
What HIPAA Auditors Check:
- ☐ BAA signed with AWS
- ☐ All data encrypted at rest and in transit
- ☐ CloudTrail logs present and immutable
- ☐ Access control (IAM) restricts to authorized personnel
- ☐ Data retention policies documented
- ☐ Incident response plan (if breach occurs)
- ☐ Regular security assessments
Evidence You Must Have:
- Signed BAA
- CloudTrail logs (minimum 1 year)
- IAM role policies
- KMS key policies
- Security audit reports
- Data handling procedures
- Training records
Common Pitfalls
Mistake 1: Not signing BAA before using Bedrock
- Result: Non-compliant from day 1
- Fix: Sign BAA before processing any patient data
Mistake 2: Logging full prompts/responses with PII
- Result: Audit logs contain unencrypted patient data
- Fix: Log only request IDs; keep sensitive data encrypted
Mistake 3: Allowing uncontrolled access to Bedrock
- Result: Unauthorized users can access patient data
- Fix: Use IAM roles to restrict access to specific users/applications
Mistake 4: Not encrypting data end-to-end
- Result: Data exposed in transit or at rest
- Fix: Use KMS encryption, enforce TLS, enable EBS encryption
Cost Estimate: HIPAA-Compliant Bedrock Setup
Monthly Costs
- Bedrock inference: ~$100-500 (depends on usage)
- KMS encryption: ~$5-20 (per key)
- CloudTrail logging: ~$5-10
- VPC Endpoint: ~$7-14
- Total: ~$120-550/month for moderate usage
One-Time Costs
- BAA negotiation: $0 (included with AWS)
- Compliance audit: $5,000-15,000
- Documentation & procedures: 10-20 hours
Real-World Example: Clinical Note Summarization
Doctor writes: "79-year-old patient with hypertension, diabetes,
presenting with chest pain radiating to left arm, shortness of breath..."
Bedrock (with encryption):
- Input encrypted with KMS
- Claude summarizes key findings
- Output encrypted
- Logged in CloudTrail
Result: Auto-summarized note in doctor's portal, compliant & auditableBottom Line
AWS Bedrock + HIPAA = Possible with proper architecture. Key requirements:
- Sign BAA
- Encrypt all data (KMS)
- Log all access (CloudTrail)
- Restrict access (IAM)
- Don’t use for treatment decisions (liability)
For healthcare organizations ready to invest in compliance, Bedrock is the best option for HIPAA-compliant AI.
AWS Cloud Architect & AI Expert
AWS-certified cloud architect and AI expert with deep expertise in cloud migrations, cost optimization, and generative AI on AWS.